mirror of
https://github.com/MicrosoftDocs/windows-itpro-docs.git
synced 2025-05-12 05:17:22 +00:00
Merge branch 'main' into vp-csp-auto2
This commit is contained in:
commit
74d473375a
66
README.md
66
README.md
@ -1,3 +1,67 @@
|
||||
# Overview
|
||||
|
||||
## Learn how to contribute
|
||||
|
||||
Anyone who is interested can contribute to the topics. When you contribute, your work will go directly into the content set after being merged. It will then be published to [Microsoft Learn](https://learn.microsoft.com/) and you will be listed as a contributor at: <https://github.com/MicrosoftDocs/windows-docs-pr/graphs/contributors>.
|
||||
|
||||
### Quickly update an article using GitHub.com
|
||||
|
||||
Contributors who only make infrequent or small updates can edit the file directly on GitHub.com without having to install any additional software. This article shows you how. [This two-minute video](https://www.microsoft.com/videoplayer/embed/RE1XQTG) also covers how to contribute.
|
||||
|
||||
1. Make sure you're signed in to GitHub.com with your GitHub account.
|
||||
2. Browse to the page you want to edit on Microsoft Learn.
|
||||
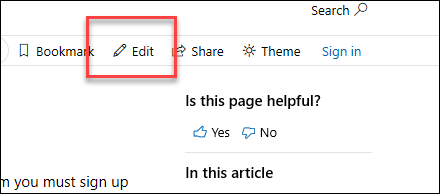
3. On the right-hand side of the page, click **Edit** (pencil icon).
|
||||
|
||||
|
||||
|
||||
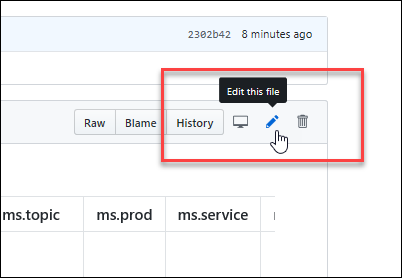
4. The corresponding topic file on GitHub opens, where you need to click the **Edit this file** pencil icon.
|
||||
|
||||
|
||||
|
||||
5. The topic opens in a line-numbered editing page where you can make changes to the file. Files in GitHub are written and edited using Markdown language. For help on using Markdown, see [Mastering Markdown](https://guides.github.com/features/mastering-markdown/). Select the **Preview changes** tab to view your changes as you go.
|
||||
|
||||
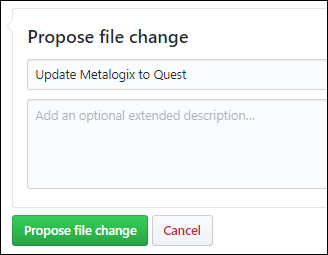
6. When you're finished making changes, go to the **Propose file change** section at the bottom of the page:
|
||||
|
||||
- A brief title is required. By default, the title is the name of the file, but you can change it.
|
||||
- Optionally, you can enter more details in the **Add an optional extended description** box.
|
||||
|
||||
When you're ready, click the green **Propose file change** button.
|
||||
|
||||
|
||||
|
||||
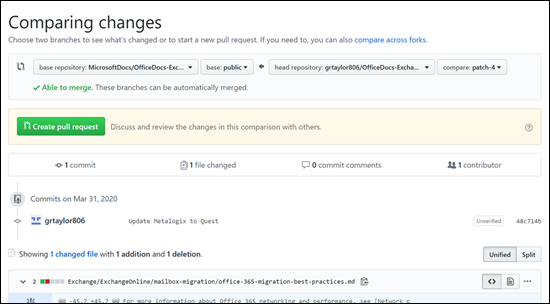
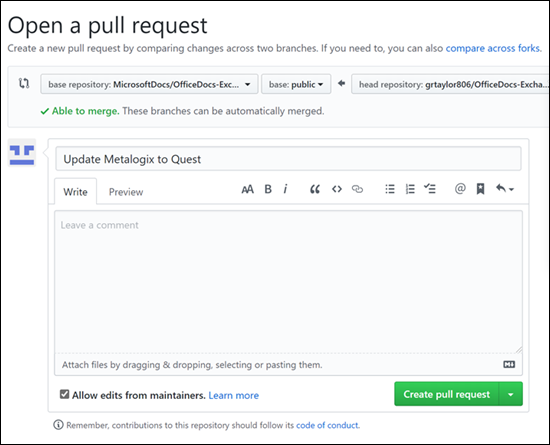
7. On the **Comparing changes** page that appears, click the green **Create pull request** button.
|
||||
|
||||
|
||||
|
||||
8. On the **Open a pull request** page that appears, click the green **Create pull request** button.
|
||||
|
||||
|
||||
|
||||
> [!NOTE]
|
||||
> Your permissions in the repo determine what you see in the last several steps. People with no special privileges will see the **Propose file change** section and subsequent confirmation pages as described. People with permissions to create and approve their own pull requests will see a similar **Commit changes** section with extra options for creating a new branch and fewer confirmation pages.<br/><br/>The point is: click any green buttons that are presented to you until there are no more.
|
||||
|
||||
The writer identified in the metadata of the topic will be notified and will eventually review and approve your changes so the topic will be updated on Microsoft Learn. If there are questions or issues with the updates, the writer will contact you.
|
||||
|
||||
## Microsoft Open Source Code of Conduct
|
||||
|
||||
This project has adopted the [Microsoft Open Source Code of Conduct](https://opensource.microsoft.com/codeofconduct/).
|
||||
For more information see the [Code of Conduct FAQ](https://opensource.microsoft.com/codeofconduct/faq/) or contact [opencode@microsoft.com](mailto:opencode@microsoft.com) with any additional questions or comments.
|
||||
|
||||
For more information see the [Code of Conduct FAQ](https://opensource.microsoft.com/codeofconduct/faq/) or contact [opencode@microsoft.com](mailto:opencode@microsoft.com) with any additional questions or comments.
|
||||
|
||||
### Contributing
|
||||
|
||||
This project welcomes contributions and suggestions. Most contributions require you to agree to a Contributor License Agreement (CLA) declaring that you have the right to, and actually do, grant us the rights to use your contribution. For details, visit <https://cla.microsoft.com>.
|
||||
|
||||
When you submit a pull request, a CLA-bot will automatically determine whether you need to provide a CLA and decorate the PR appropriately (e.g., label, comment). Simply follow the instructions provided by the bot. You will only need to do this once across all repos using our CLA.
|
||||
|
||||
### Legal Notices
|
||||
|
||||
Microsoft and any contributors grant you a license to the Microsoft documentation and other content in this repository under the [Creative Commons Attribution 4.0 International Public License](https://creativecommons.org/licenses/by/4.0/legalcode), see the [LICENSE](LICENSE) file, and grant you a license to any code in the repository under the [MIT License](https://opensource.org/licenses/MIT), see the [LICENSE-CODE](LICENSE-CODE) file.
|
||||
|
||||
Microsoft, Windows, Microsoft Azure and/or other Microsoft products and services referenced in the documentation may be either trademarks or registered trademarks of Microsoft in the United States and/or other countries.
|
||||
|
||||
The licenses for this project do not grant you rights to use any Microsoft names, logos, or trademarks. Microsoft's general trademark guidelines can be found at <https://go.microsoft.com/fwlink/?LinkID=254653>.
|
||||
|
||||
Privacy information can be found at <https://privacy.microsoft.com/>
|
||||
|
||||
Microsoft and any contributors reserve all others rights, whether under their respective copyrights, patents, or trademarks, whether by implication, estoppel or otherwise.
|
||||
|
||||
@ -220,7 +220,7 @@ The most common values:
|
||||
| 0x14 | KDC\_ERR\_TGT\_REVOKED | TGT has been revoked | Since the remote KDC may change its PKCROSS key while there are PKCROSS tickets still active, it SHOULD cache the old PKCROSS keys until the last issued PKCROSS ticket expires. Otherwise, the remote KDC will respond to a client with a KRB-ERROR message of type KDC\_ERR\_TGT\_REVOKED. See [RFC1510](https://www.ietf.org/proceedings/49/I-D/draft-ietf-cat-kerberos-pk-cross-07.txt) for more details. |
|
||||
| 0x15 | KDC\_ERR\_CLIENT\_NOTYET | Client not yet valid—try again later | No information. |
|
||||
| 0x16 | KDC\_ERR\_SERVICE\_NOTYET | Server not yet valid—try again later | No information. |
|
||||
| 0x17 | KDC\_ERR\_KEY\_EXPIRED | Password has expired—change password to reset | The user’s password has expired.<br>This error code cannot occur in event “[4768](event-4768.md). A Kerberos authentication ticket (TGT) was requested”. It occurs in “[4771](event-4771.md). Kerberos pre-authentication failed” event. |
|
||||
| 0x17 | KDC\_ERR\_KEY\_EXPIRED | Password has expired—change password to reset | The user’s password has expired. |
|
||||
| 0x18 | KDC\_ERR\_PREAUTH\_FAILED | Pre-authentication information was invalid | The wrong password was provided.<br>This error code cannot occur in event “[4768](event-4768.md). A Kerberos authentication ticket (TGT) was requested”. It occurs in “[4771](event-4771.md). Kerberos pre-authentication failed” event. |
|
||||
| 0x19 | KDC\_ERR\_PREAUTH\_REQUIRED | Additional pre-authentication required | This error often occurs in UNIX interoperability scenarios. MIT-Kerberos clients do not request pre-authentication when they send a KRB\_AS\_REQ message. If pre-authentication is required (the default), Windows systems will send this error. Most MIT-Kerberos clients will respond to this error by giving the pre-authentication, in which case the error can be ignored, but some clients might not respond in this way. |
|
||||
| 0x1A | KDC\_ERR\_SERVER\_NOMATCH | KDC does not know about the requested server | No information. |
|
||||
|
||||
@ -8,7 +8,7 @@ ms.pagetype: security
|
||||
ms.localizationpriority: medium
|
||||
author: vinaypamnani-msft
|
||||
ms.author: vinpa
|
||||
ms.date: 09/09/2021
|
||||
ms.date: 11/30/2022
|
||||
ms.reviewer:
|
||||
manager: aaroncz
|
||||
ms.custom: asr
|
||||
@ -28,10 +28,12 @@ ms.topic: how-to
|
||||
## Review system requirements
|
||||
|
||||
See [System requirements for Microsoft Defender Application Guard](./reqs-md-app-guard.md) to review the hardware and software installation requirements for Microsoft Defender Application Guard.
|
||||
>[!NOTE]
|
||||
>Microsoft Defender Application Guard is not supported on VMs and VDI environment. For testing and automation on non-production machines, you may enable WDAG on a VM by enabling Hyper-V nested virtualization on the host.
|
||||
|
||||
> [!NOTE]
|
||||
> Microsoft Defender Application Guard is not supported on VMs and VDI environment. For testing and automation on non-production machines, you may enable WDAG on a VM by enabling Hyper-V nested virtualization on the host.
|
||||
|
||||
## Prepare for Microsoft Defender Application Guard
|
||||
|
||||
Before you can install and use Microsoft Defender Application Guard, you must determine which way you intend to use it in your enterprise. You can use Application Guard in either **Standalone** or **Enterprise-managed** mode.
|
||||
|
||||
### Standalone mode
|
||||
@ -52,6 +54,7 @@ Applies to:
|
||||
You and your security department can define your corporate boundaries by explicitly adding trusted domains and by customizing the Application Guard experience to meet and enforce your needs on employee devices. Enterprise-managed mode also automatically redirects any browser requests to add non-enterprise domain(s) in the container.
|
||||
|
||||
The following diagram shows the flow between the host PC and the isolated container.
|
||||
|
||||

|
||||
|
||||
## Install Application Guard
|
||||
@ -60,22 +63,22 @@ Application Guard functionality is turned off by default. However, you can quick
|
||||
|
||||
### To install by using the Control Panel
|
||||
|
||||
1. Open the **Control Panel**, click **Programs,** and then click **Turn Windows features on or off**.
|
||||
1. Open the **Control Panel**, click **Programs,** and then select **Turn Windows features on or off**.
|
||||
|
||||

|
||||
|
||||
2. Select the check box next to **Microsoft Defender Application Guard** and then click **OK**.
|
||||
2. Select the check box next to **Microsoft Defender Application Guard** and then select **OK**.
|
||||
|
||||
Application Guard and its underlying dependencies are all installed.
|
||||
|
||||
### To install by using PowerShell
|
||||
|
||||
>[!NOTE]
|
||||
>Ensure your devices have met all system requirements prior to this step. PowerShell will install the feature without checking system requirements. If your devices don't meet the system requirements, Application Guard may not work. This step is recommended for enterprise managed scenarios only.
|
||||
> [!NOTE]
|
||||
> Ensure your devices have met all system requirements prior to this step. PowerShell will install the feature without checking system requirements. If your devices don't meet the system requirements, Application Guard may not work. This step is recommended for enterprise managed scenarios only.
|
||||
|
||||
1. Click the **Search** or **Cortana** icon in the Windows 10 or Windows 11 taskbar and type **PowerShell**.
|
||||
1. Select the **Search** or **Cortana** icon in the Windows 10 or Windows 11 taskbar and type **PowerShell**.
|
||||
|
||||
2. Right-click **Windows PowerShell**, and then click **Run as administrator**.
|
||||
2. Right-click **Windows PowerShell**, and then select **Run as administrator**.
|
||||
|
||||
Windows PowerShell opens with administrator credentials.
|
||||
|
||||
@ -95,17 +98,15 @@ Application Guard functionality is turned off by default. However, you can quick
|
||||
|
||||
:::image type="content" source="images/MDAG-EndpointMgr-newprofile.jpg" alt-text="Enroll devices in Intune.":::
|
||||
|
||||
1. Sign in to the [Microsoft Endpoint Manager admin center](https://go.microsoft.com/fwlink/?linkid=2109431).
|
||||
|
||||
1. Choose **Devices** > **Configuration profiles** > **+ Create profile**, and do the following: <br/>
|
||||
1. In the [Microsoft Endpoint Manager admin center](https://go.microsoft.com/fwlink/?linkid=2109431), choose **Devices** > **Configuration profiles** > **+ Create profile**, and do the following: <br/>
|
||||
|
||||
1. In the **Platform** list, select **Windows 10 and later**.
|
||||
|
||||
1. In the **Profile** list, select **Endpoint protection**.
|
||||
2. In the **Profile** type, choose **Templates** and select **Endpoint protection**.
|
||||
|
||||
1. Choose **Create**.
|
||||
3. Choose **Create**.
|
||||
|
||||
1. Specify the following settings for the profile:
|
||||
2. Specify the following settings for the profile:
|
||||
|
||||
- **Name** and **Description**
|
||||
|
||||
@ -115,16 +116,16 @@ Application Guard functionality is turned off by default. However, you can quick
|
||||
|
||||
- Choose your preferences for **Clipboard behavior**, **External content**, and the remaining settings.
|
||||
|
||||
1. Choose **OK**, and then choose **OK** again.
|
||||
3. Choose **OK**, and then choose **OK** again.
|
||||
|
||||
1. Review your settings, and then choose **Create**.
|
||||
4. Review your settings, and then choose **Create**.
|
||||
|
||||
1. Choose **Assignments**, and then do the following:
|
||||
5. Choose **Assignments**, and then do the following:
|
||||
|
||||
1. On the **Include** tab, in the **Assign to** list, choose an option.
|
||||
|
||||
1. If you have any devices or users you want to exclude from this endpoint protection profile, specify those on the **Exclude** tab.
|
||||
2. If you have any devices or users you want to exclude from this endpoint protection profile, specify those on the **Exclude** tab.
|
||||
|
||||
1. Click **Save**.
|
||||
3. Select **Save**.
|
||||
|
||||
After the profile is created, any devices to which the policy should apply will have Microsoft Defender Application Guard enabled. Users might have to restart their devices in order for protection to be in place.
|
||||
|
||||
Loading…
x
Reference in New Issue
Block a user