| Enable device setup if you want to configure settings on this page.**If enabled:**Enter a name for the device.(Optional) Select a license file to upgrade Windows 10 to a different edition. [See the permitted upgrades.](https://technet.microsoft.com/itpro/windows/deploy/windows-10-edition-upgrades)Toggle **Configure devices for shared use** off. This setting optimizes Windows 10 for shared use scenarios and isn't necessary for a kiosk scenario.You can also select to remove pre-installed software from the device. |  |
|  Enable network setup if you want to configure settings on this page.**If enabled:**Toggle **On** or **Off** for wireless network connectivity. If you select **On**, enter the SSID, the network type (**Open** or **WPA2-Personal**), and (if **WPA2-Personal**) the password for the wireless network. |  |
|  Enable account management if you want to configure settings on this page. **If enabled:**You can enroll the device in Active Directory, enroll in Azure Active Directory, or create a local administrator account on the deviceTo enroll the device in Active Directory, enter the credentials for a least-privileged user account to join the device to the domain.Before you use a Windows Configuration Designer wizard to configure bulk Azure AD enrollment, [set up Azure AD join in your organization](https://docs.microsoft.com/azure/active-directory/active-directory-azureadjoin-setup). The **maximum number of devices per user** setting in your Azure AD tenant determines how many times the bulk token that you get in the wizard can be used. To enroll the device in Azure AD, select that option and enter a friendly name for the bulk token you will get using the wizard. Set an expiration date for the token (maximum is 30 days from the date you get the token). Click **Get bulk token**. In the **Let's get you signed in** window, enter an account that has permissions to join a device to Azure AD, and then the password. Click **Accept** to give Windows Configuration Designer the necessary permissions.**Warning:** You must run Windows Configuration Designer on Windows 10 to configure Azure Active Directory enrollment using any of the wizards.To create a local administrator account, select that option and enter a user name and password. **Important:** If you create a local account in the provisioning package, you must change the password using the **Settings** app every 42 days. If the password is not changed during that period, the account might be locked out and unable to sign in. |  |
|  You can provision the kiosk app in the **Add applications** step. You can install multiple applications, both Classic Windows (Win32) apps and Universal Windows Platform (UWP) apps, in a provisioning package. The settings in this step vary according to the application that you select. For help with the settings, see [Provision PCs with apps](provisioning-packages/provision-pcs-with-apps.md)**Warning:** If you click the plus button to add an application, you must specify an application for the provisioning package to validate. If you click the plus button in error, select any executable file in **Installer Path**, and then a **Cancel** button becomes available, allowing you to complete the provisioning package without an application. |  |
|  To provision the device with a certificate for the kiosk app, click **Add a certificate**. Enter a name for the certificate, and then browse to and select the certificate to be used. |  |
|  You can create a local standard user account that will be used to run the kiosk app. If you toggle **No**, make sure that you have an existing user account to run the kiosk app.If you want to create an account, enter the user name and password, and then toggle **Yes** or **No** to automatically sign in the account when the device starts.In **Configure the kiosk mode app**, enter the name of the user account that will run the kiosk mode app. Select the type of app to run in kiosk mode, and then enter the path or filename (for a Classic Windows app) or the AUMID (for a Universal Windows app). For a Classic Windows app, you can use the filename if the path to the file is in the PATH environment variable, otherwise the full path is required. |  |
|  On this step, select your options for tablet mode, the user experience on the Welcome and shutdown screens, and the timeout settings. |  |
| You can set a password to protect your provisioning package. You must enter this password when you apply the provisioning package to a device. | 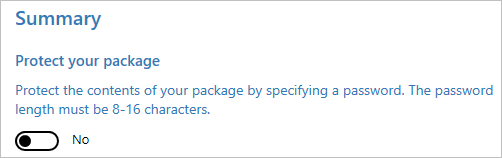 |
>[!NOTE]
>If you want to use [the advanced editor in Windows Configuration Designer](provisioning-packages/provisioning-create-package.md#configure-settings), specify the user account and app (by AUMID) in **Runtime settings** > **AssignedAccess** > **AssignedAccessSettings**
>[!TIP]
>You can also use [an XML file to configure both multi-app and single-app kiosks.](lock-down-windows-10-to-specific-apps.md)
>[!IMPORTANT]
>When you build a provisioning package, you may include sensitive information in the project files and in the provisioning package (.ppkg) file. Although you have the option to encrypt the .ppkg file, project files are not encrypted. You should store the project files in a secure location and delete the project files when they are no longer needed.
[Learn how to apply a provisioning package.](provisioning-packages/provisioning-apply-package.md)
## Set up a kiosk or digital sign in Intune or other MDM service
>App type: UWP
>
>OS edition: Windows 10 Pro (version 1709), Ent, Edu
>
>Account type: Local standard user, Azure AD
Microsoft Intune and other MDM services enable kiosk configuration through the [AssignedAccess configuration service provider (CSP)](https://docs.microsoft.com/windows/client-management/mdm/assignedaccess-csp). Assigned Access has a KioskModeApp setting. In the KioskModeApp setting, you enter the user account name and [AUMID](https://docs.microsoft.com/windows-hardware/customize/enterprise/find-the-application-user-model-id-of-an-installed-app) for the app to run in kiosk mode.
The following steps explain how to configure a kiosk in Microsoft Intune. For other MDM services, see the documentation for your provider.
**To configure kiosk in Microsoft Intune**
2. In the Microsoft Azure portal, search for **Intune** or go to **More services** > **Intune**.
3. Select **Device configuration**.
4. Select **Profiles**.
5. Select **Create profile**.
6. Enter a friendly name for the profile.
7. Select **Windows 10 and later** for the platform.
8. Select **Kiosk (Preview)** for the profile type.
9. Enter a friendly name for the kiosk configuration.
10. Select **Kiosk - 1 setting available**.
10. Select **Add** to add a kiosk configuration.
10. Enter a friendly name for the kiosk configuration, and then in **Kiosk Mode**, select **Single full-screen app kiosk**.
10. Select either **Select a managed app** to choose a kiosk app that is managed by Intune, or **Enter UWP app AUMID** to specify the kiosk app by AUMID, and then select the app or enter the AUMID as appropriate.
1. For the user account, select either **Autologon** to create a user account for the kiosk that will sign in automatically, or **Local user account** to configure an existing user account to run the kiosk. **Local user account** can be a local standard user account on the device or an Azure Active Directory account.
14. Select **OK**, and then select **Create**.
18. Assign the profile to a device group to configure the devices in that group as kiosks.