2.8 KiB
title, description, keywords, ms.prod, ms.mktglfcycl, ms.sitesec, ms.localizationpriority, ms.author, author, ms.date
| title | description | keywords | ms.prod | ms.mktglfcycl | ms.sitesec | ms.localizationpriority | ms.author | author | ms.date |
|---|---|---|---|---|---|---|---|---|---|
| Worms | Learn about worms, how they infect devices and what you can do to protect yourself. | security, malware | w10 | secure | library | medium | dansimp | dansimp | 07/01/2018 |
Worms
A worm is a type of malware that spreads to other PCs. Worms can copy themselves and often spread through a PC network by exploiting security vulnerabilities. They can spread through email attachments, instant messaging programs, file-sharing programs, social networking sites, network shares, removable drives, and software vulnerabilities.
How worms work
Worms represent a large category of malware. Different worms use different methods to infect devices. Depending on the variant, they can steal sensitive information, change PC security settings, send information to malicious hackers, stop users from accessing files, and other malicious acts.
Jenxcus (also known as Dunihi), Gamarue (also known as Androm), and Bondat have consistently remained at the top of the list of malware that infect users running Microsoft security software. Although these worms share some commonalities, it is interesting to note that they also have distinct characteristics.
Jenxcus has capabilities of not only infecting removable drives but can also act as a backdoor that connects back to its server. This threat typically gets into a PC from a drive-by download attack, meaning it's installed when users just visit a compromised webpage.
Gamarue typically arrives through spam campaigns, exploits, downloaders, social networking sites, and removable drives. When Gamarue infects a PC, it becomes a distribution channel for other malware. We’ve seen it distribute other malware such as infostealers, spammers, clickers, downloaders, and rogues.
Bondat typically arrives through fictitious Nullsoft Sciptable Install System (NSIS) Java installers and removable drives. When Bondat infects a system, it gathers information about the machine such as PC name, Globally Unique Identifier (GUID), and OS build. It then sends that information to a remote server.
Both Bondat and Gamarue have clever ways of obscuring themselves to evade detection. By hiding what they are doing on your PC they try to avoid detection by your security software.
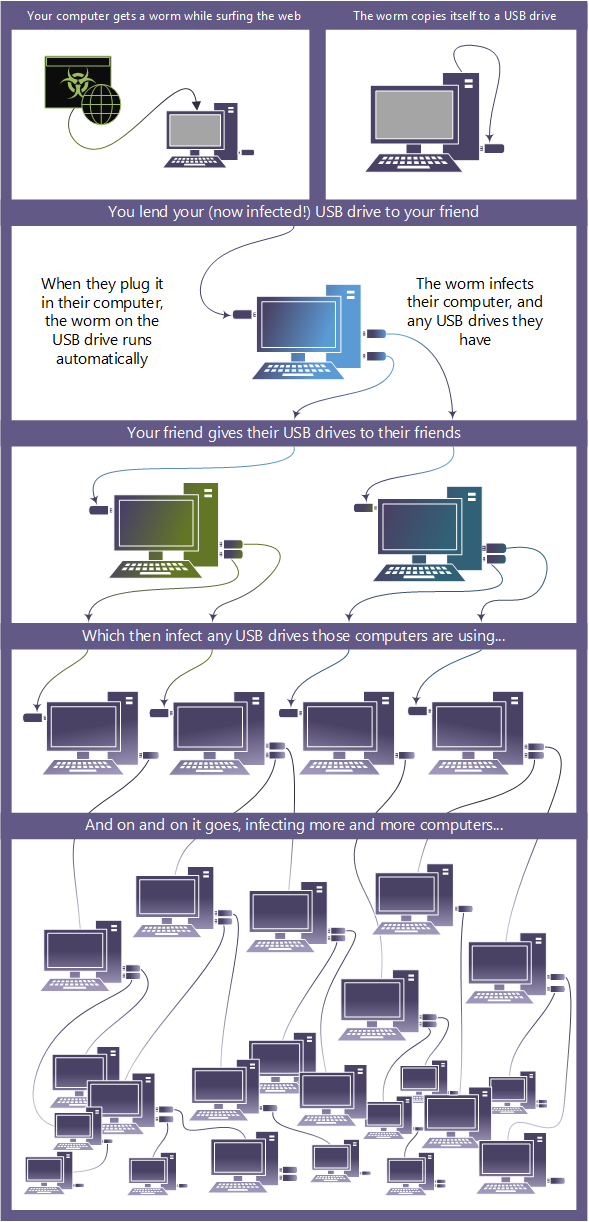
This image shows how a worm can quickly spread through a shared USB drive.
Figure worm spreading from a shared USB drive
How to protect against worms
Use the following free Microsoft software to detect and remove it:
-
Windows Defender for Windows 10, and Windows 8.1
-
Microsoft Safety Scanner for Windows 7 and Windows Vista
You should also run a full scan find other, hidden malware. If you still can't remove it, visit our advanced troubleshooting page for more help.