36 KiB
title, description, ms.assetid, ms.prod, ms.mktglfcycl, ms.sitesec, ms.pagetype, author, localizationpriority
| title | description | ms.assetid | ms.prod | ms.mktglfcycl | ms.sitesec | ms.pagetype | author | localizationpriority |
|---|---|---|---|---|---|---|---|---|
| Create a Windows Information Protection (WIP) policy using Microsoft Intune (Windows 10) | Microsoft Intune helps you create and deploy your Windows Information Protection (WIP) policy, including letting you choose your protected apps, your WIP-protection level, and how to find enterprise data on the network. | 4b307c99-3016-4d6a-9ae7-3bbebd26e721 | w10 | explore | library | security | eross-msft | high |
Create a Windows Information Protection (WIP) policy using Microsoft Intune
Applies to:
- Windows 10, version 1607
- Windows 10 Mobile
Microsoft Intune helps you create and deploy your Windows Information Protection (WIP) policy, including letting you choose your allowed apps, your WIP-protection level, and how to find enterprise data on the network.
Important note about the June service update for Insider Preview
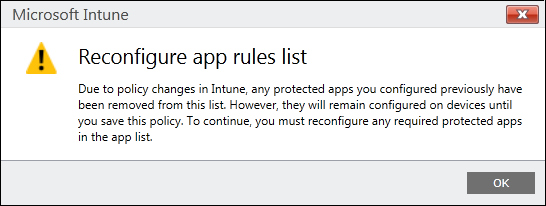
We've received some great feedback from you, our Windows 10 Insider Preview customers, about our Windows Information Protection experiences and processes. Because of that feedback, we're delighted to deliver an enhanced apps policy experience with the June service update. This means that when you open an existing Windows Information Protection policy after we release the June service update in your test environment, your existing Windows 10 Windows Information Protection app rules (formerly in the Protected Apps area) will be removed.
To prepare for this change, we recommend that you make an immediate backup of your current app rules as they are today, so you can use them to help reconfigure your app rules with the enhanced experience. When you open an existing Windows Information Protection policy after we release the June service update, you'll get a dialog box telling you about this change. Click the OK button to close the box and to begin reconfiguring your app rules.
Note that if you exit the Policy page before you've saved your new policy, your existing deployments won't be affected. However, if you save the policy without reconfiguring your apps, an updated policy will be deployed to your employees with an empty app rules list.
Add a WIP policy
After you’ve set up Intune for your organization, you must create a WIP-specific policy.
To add a WIP policy
-
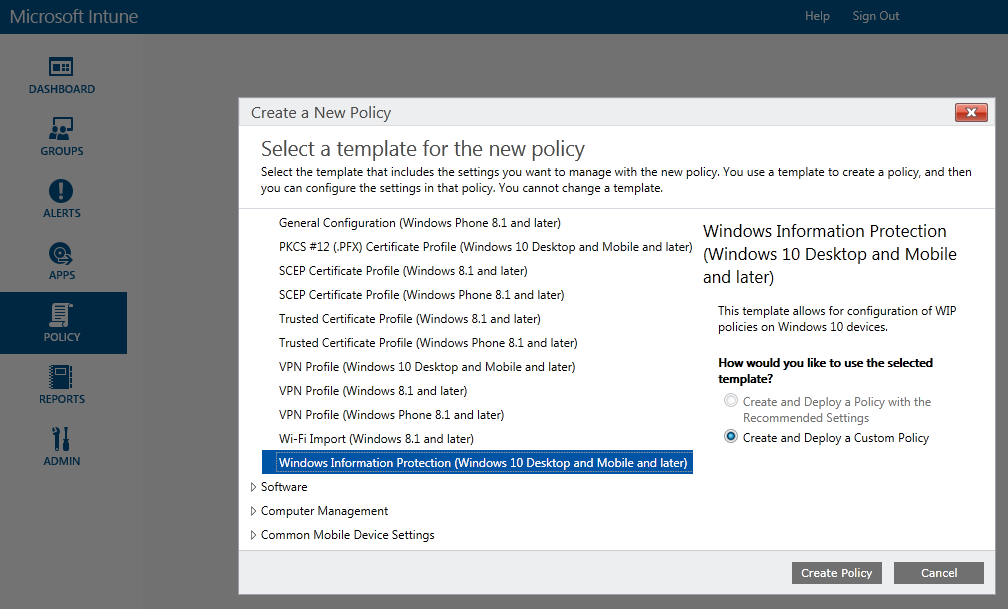
Open the Intune administration console, and go to the Policy node, and then click Add Policy from the Tasks area.
-
Go to Windows, click the Windows Information Protection (Windows 10 Desktop and Mobile and later) policy, click Create and Deploy a Custom Policy, and then click Create Policy.
-
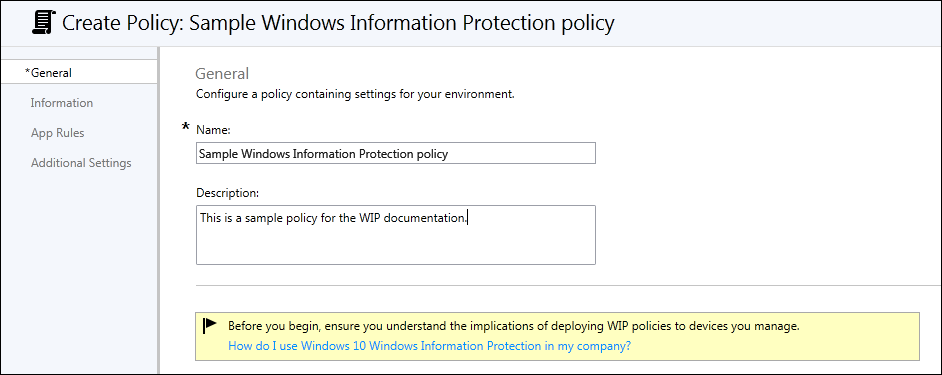
Type a name (required) and an optional description for your policy into the Name and Description boxes.
Add app rules to your policy
During the policy-creation process in Intune, you can choose the apps you want to give access to your enterprise data through WIP. Apps included in this list can protect data on behalf of the enterprise and are restricted from copying or moving enterprise data to unprotected apps.
The steps to add your app rules are based on the type of rule template being applied. You can add a store app (also known as a Universal Windows Platform (UWP) app), a signed Windows desktop app, or an AppLocker policy file.
Important
WIP-aware apps are expected to prevent enterprise data from going to unprotected network locations and to avoid encrypting personal data. On the other hand, WIP-unaware apps might not respect the corporate network boundary, and WIP-unaware apps will encrypt all files they create or modify. This means that they could encrypt personal data and cause data loss during the revocation process.
Care must be taken to get a support statement from the software provider that their app is safe with WIP before adding it to your App Rules list. If you don’t get this statement, it’s possible that you could experience app compat issues due to an app losing the ability to access a necessary file after revocation.
Note
If you want to use File hash or Path rules, instead of Publisher rules, you must follow the steps in the Add apps to your Windows Information Protection (WIP) policy by using the Microsoft Intune custom URI functionality topic.
Add a store app rule to your policy
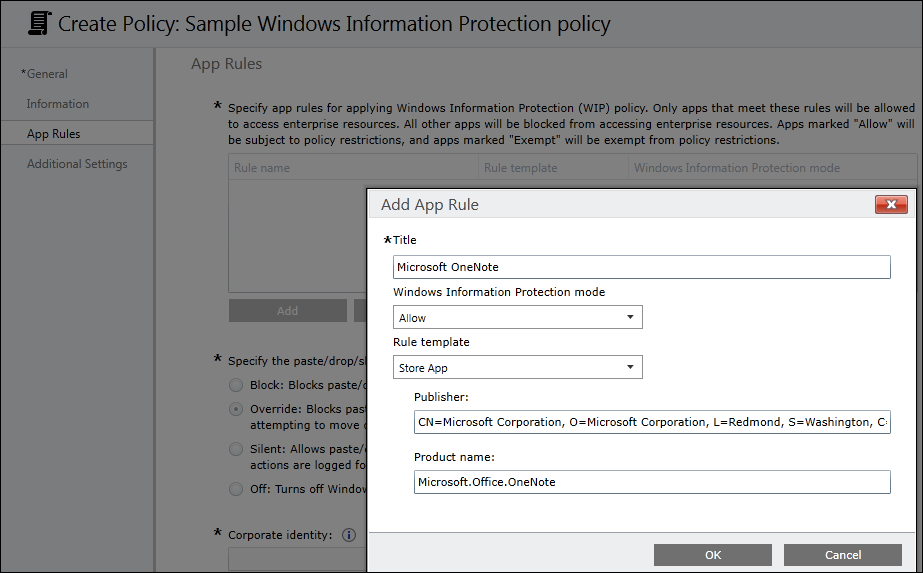
For this example, we’re going to add Microsoft OneNote, a store app, to the App Rules list.
To add a store app
-
From the App Rules area, click Add.
The Add App Rule box appears.
-
Add a friendly name for your app into the Title box. In this example, it’s Microsoft OneNote.
-
Click Allow from the Windows Information Protection mode drop-down list.
Allow turns on WIP, helping to protect that app’s corporate data through the enforcement of WIP restrictions. Instructions for exempting an app are included in the Exempt apps from WIP restrictions section of this topic.
-
Pick Store App from the Rule template drop-down list.
The box changes to show the store app rule options.
-
Type the name of the app and the name of its publisher, and then click OK. For this UWP app example, the Publisher is
CN=Microsoft Corporation, O=Microsoft Corporation, L=Redmond, S=Washington, C=USand the Product name isMicrosoft.Office.OneNote.
If you don't know the publisher or product name, you can find them for both desktop devices and Windows 10 Mobile phones by following these steps.
To find the Publisher and Product Name values for Store apps without installing them
-
Go to the Windows Store for Business website, and find your app. For example, Microsoft OneNote.
Note
If your app is already installed on desktop devices, you can use the AppLocker local security policy MMC snap-in to gather the info for adding the app to the protected apps list. For info about how to do this, see the Add apps to your Windows Information Protection (WIP) policy by using the Microsoft Intune custom URI functionality topic.
-
Copy the ID value from the app URL. For example, Microsoft OneNote's ID URL is https://www.microsoft.com/store/apps/onenote/9wzdncrfhvjl, and you'd copy the ID value,
9wzdncrfhvjl. -
In a browser, run the Store for Business portal web API, to return a JavaScript Object Notation (JSON) file that includes the publisher and product name values. For example, run https://bspmts.mp.microsoft.com/v1/public/catalog/Retail/Products/9wzdncrfhvjl/applockerdata, where
9wzdncrfhvjlis replaced with your ID value.The API runs and opens a text editor with the app details.
{ "packageIdentityName": "Microsoft.Office.OneNote", "publisherCertificateName": "CN=Microsoft Corporation, O=Microsoft Corporation, L=Redmond, S=Washington, C=US" } -
Copy the
publisherCertificateNamevalue into the Publisher Name box and copy thepackageIdentityNamevalue into the Product Name box of Intune.Important
The JSON file might also return a
windowsPhoneLegacyIdvalue for both the Publisher Name and Product Name boxes. This means that you have an app that’s using a XAP package and that you must set the Product Name aswindowsPhoneLegacyId, and set the Publisher Name asCN=followed by thewindowsPhoneLegacyId.For example:
{ "windowsPhoneLegacyId": "ca05b3ab-f157-450c-8c49-a1f127f5e71d", }
To find the Publisher and Product Name values for apps installed on Windows 10 mobile phones
-
If you need to add mobile apps that aren't distributed through the Store for Business, you must use the Windows Device Portal feature.
Note
Your PC and phone must be on the same wireless network.
-
On the Windows Phone, go to Settings, choose Update & security, and then choose For developers.
-
In the For developers screen, turn on Developer mode, turn on Device Discovery, and then turn on Device Portal.
-
Copy the URL in the Device Portal area into your device's browser, and then accept the SSL certificate.
-
In the Device discovery area, press Pair, and then enter the PIN into the website from the previous step.
-
On the Apps tab of the website, you can see details for the running apps, including the publisher and product names.
-
Start the app for which you're looking for the publisher and product name values.
-
Copy the
publisherCertificateNamevalue and paste it into the Publisher Name box and thepackageIdentityNamevalue into the Product Name box of Intune.Important
The JSON file might also return a
windowsPhoneLegacyIdvalue for both the Publisher Name and Product Name boxes. This means that you have an app that’s using a XAP package and that you must set the Product Name aswindowsPhoneLegacyId, and set the Publisher Name asCN=followed by thewindowsPhoneLegacyId.For example:
{ "windowsPhoneLegacyId": "ca05b3ab-f157-450c-8c49-a1f127f5e71d", }
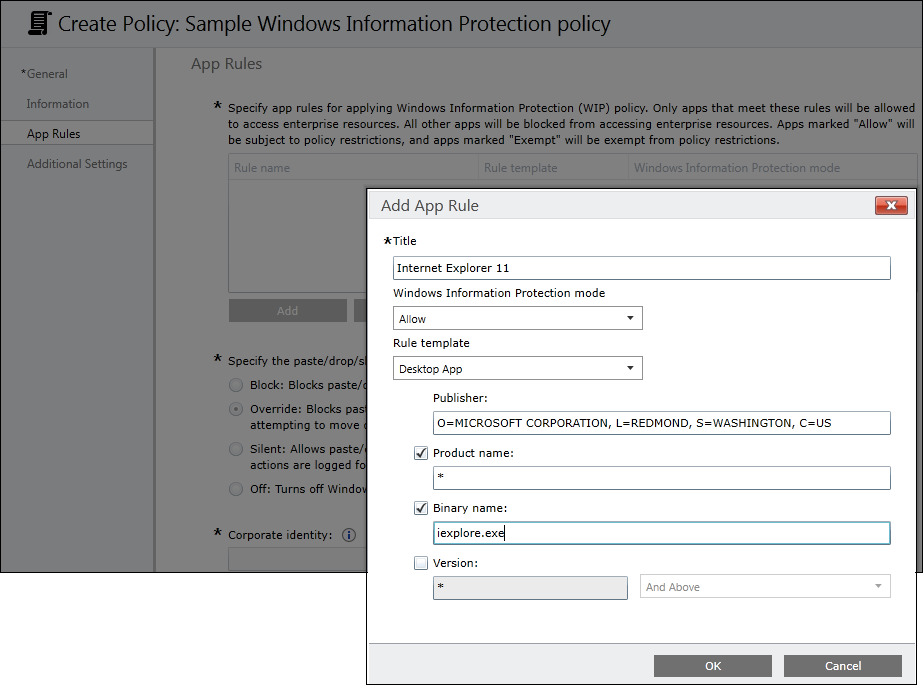
Add a desktop app rule to your policy
For this example, we’re going to add Internet Explorer, a desktop app, to the App Rules list.
To add a desktop app
-
From the App Rules area, click Add.
The Add App Rule box appears.
-
Add a friendly name for your app into the Title box. In this example, it’s Internet Explorer.
-
Click Allow from the Windows Information Protection mode drop-down list.
Allow turns on WIP, helping to protect that app’s corporate data through the enforcement of WIP restrictions. Instructions for exempting an app are included in the Exempt apps from WIP restrictions section of this topic.
-
Pick Desktop App from the Rule template drop-down list.
The box changes to show the store app rule options.
-
Pick the options you want to include for the app rule (see table), and then click OK.
Option Manages All fields left as “*” All files signed by any publisher. (Not recommended) Publisher selected All files signed by the named publisher. This might be useful if your company is the publisher and signer of internal line-of-business apps.
Publisher and Product Name selected All files for the specified product, signed by the named publisher. Publisher, Product Name, and Binary name selected Any version of the named file or package for the specified product, signed by the named publisher. Publisher, Product Name, Binary name, and File Version, and above, selected Specified version or newer releases of the named file or package for the specified product, signed by the named publisher. This option is recommended for enlightened apps that weren't previously enlightened.
Publisher, Product Name, Binary name, and File Version, And below selected Specified version or older releases of the named file or package for the specified product, signed by the named publisher. Publisher, Product Name, Binary name, and File Version, Exactly selected Specified version of the named file or package for the specified product, signed by the named publisher.
If you’re unsure about what to include for the publisher, you can run this PowerShell command:
Get-AppLockerFileInformation -Path "<path of the exe>"
Where "<path of the exe>" goes to the location of the app on the device. For example, Get-AppLockerFileInformation -Path "C:\Program Files\Internet Explorer\iexplore.exe".
In this example, you'd get the following info:
Path Publisher
---- ---------
%PROGRAMFILES%\INTERNET EXPLORER\IEXPLORE.EXE O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US\INTERNET EXPLOR...
Where the text, O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US is the publisher name to enter in the Publisher Name box.
Add an AppLocker policy file
For this example, we’re going to add an AppLocker XML file to the App Rules list. You’ll use this option if you want to add multiple apps at the same time. For more info about AppLocker, see the AppLocker content.
To create an app rule and xml file using the AppLocker tool
-
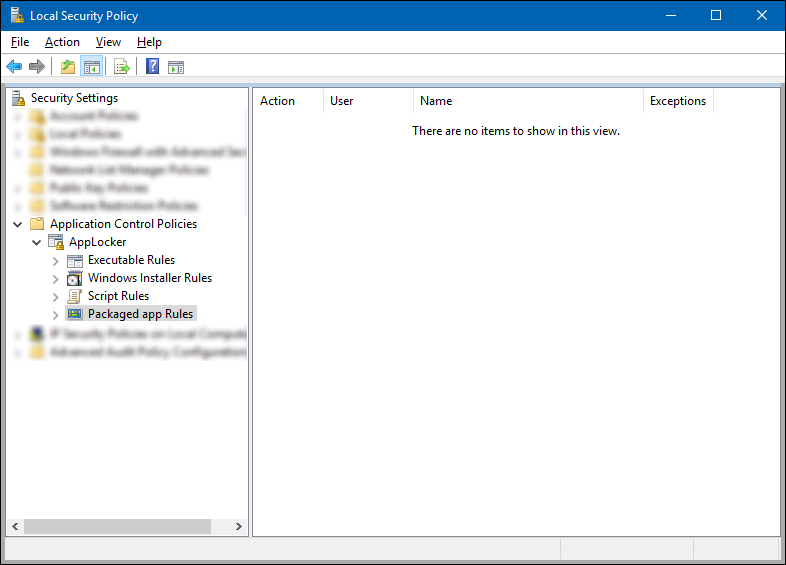
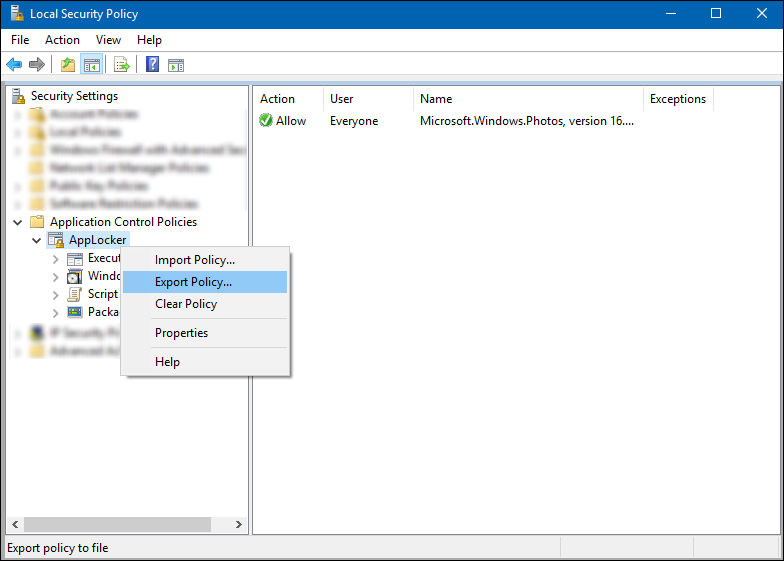
Open the Local Security Policy snap-in (SecPol.msc).
-
In the left pane, expand Application Control Policies, expand AppLocker, and then click Packaged App Rules.
-
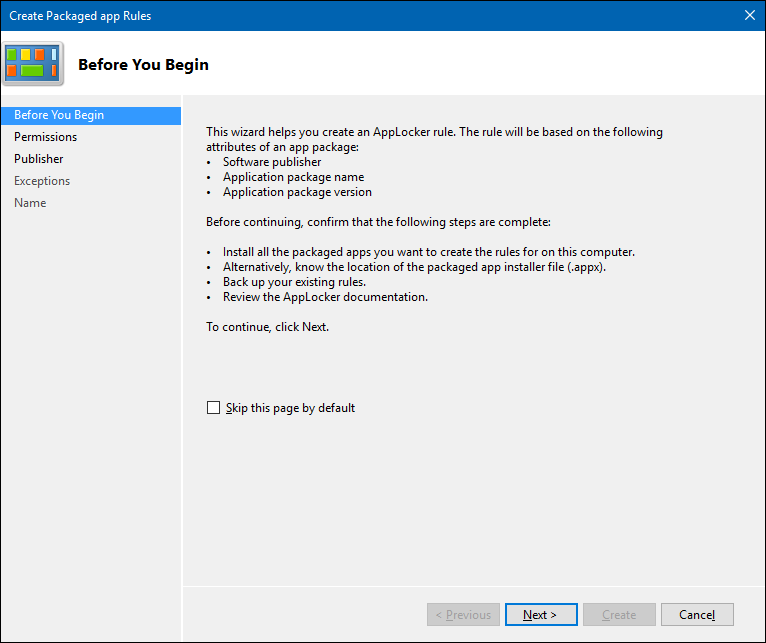
Right-click in the right-hand pane, and then click Create New Rule.
The Create Packaged app Rules wizard appears.
-
On the Before You Begin page, click Next.
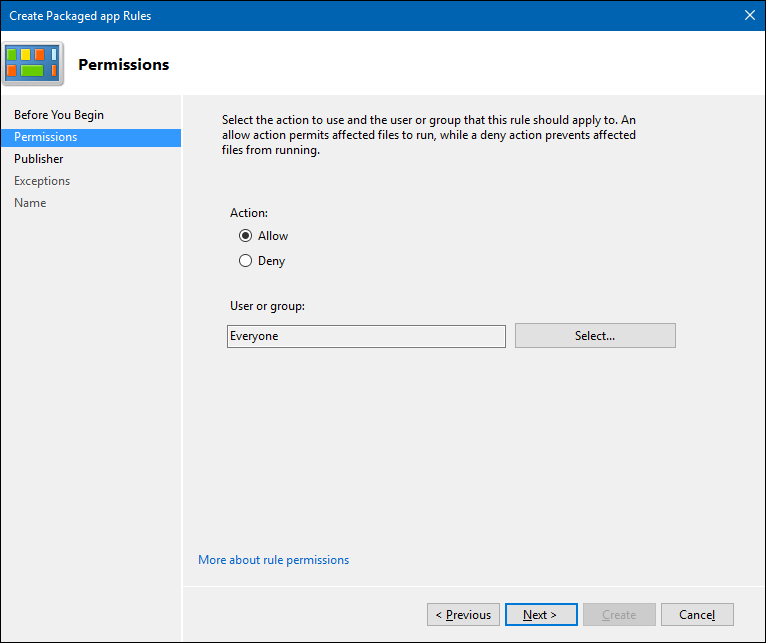
-
On the Permissions page, make sure the Action is set to Allow and the User or group is set to Everyone, and then click Next.
-
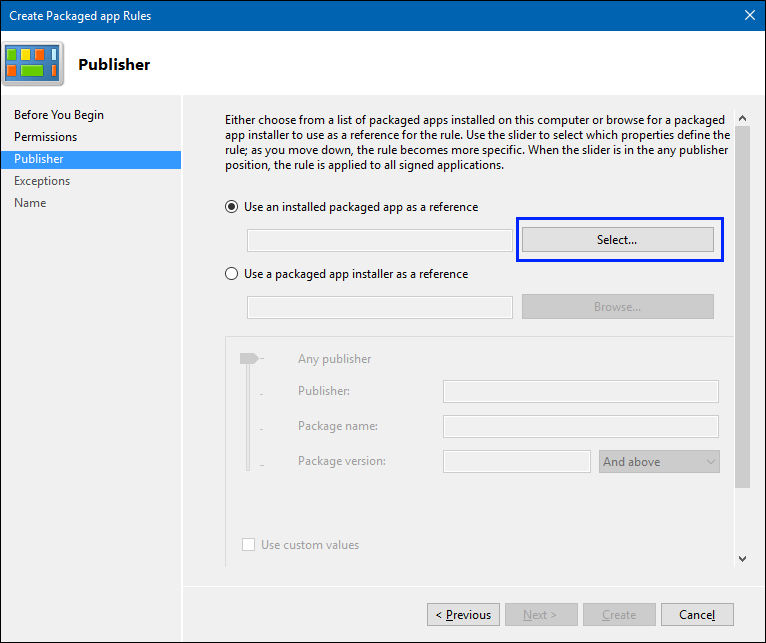
On the Publisher page, click Select from the Use an installed packaged app as a reference area.
-
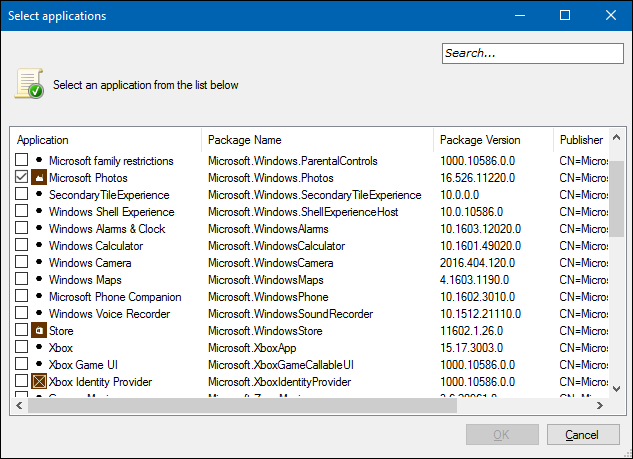
In the Select applications box, pick the app that you want to use as the reference for your rule, and then click OK. For this example, we’re using Microsoft Photos.
-
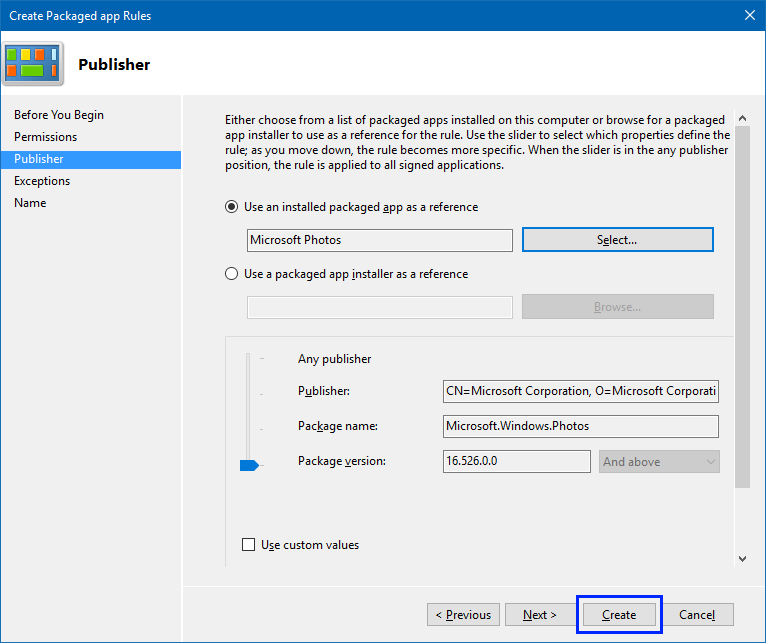
On the updated Publisher page, click Create.
-
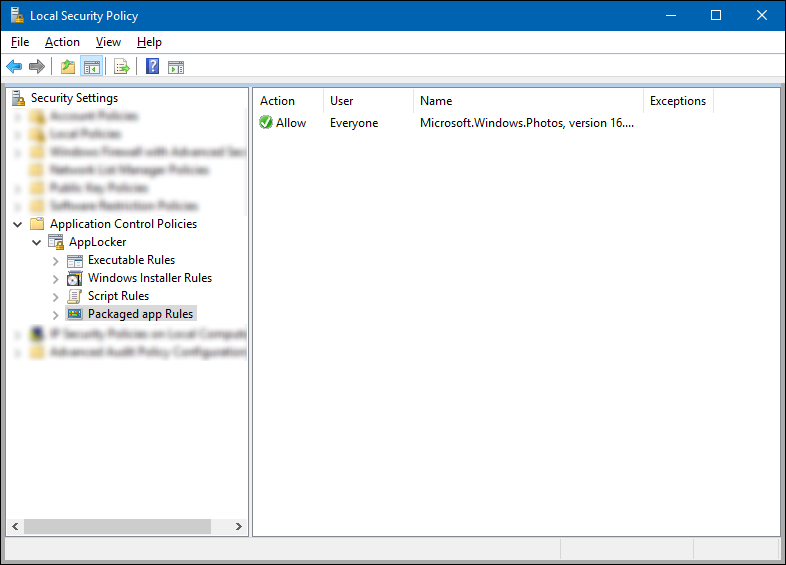
Review the Local Security Policy snap-in to make sure your rule is correct.
-
In the left pane, right-click on AppLocker, and then click Export policy.
The Export policy box opens, letting you export and save your new policy as XML.
-
In the Export policy box, browse to where the policy should be stored, give the policy a name, and then click Save.
The policy is saved and you’ll see a message that says 1 rule was exported from the policy.
Example XML file
This is the XML file that AppLocker creates for Microsoft Photos.<AppLockerPolicy Version="1"> <RuleCollection Type="Exe" EnforcementMode="NotConfigured" /> <RuleCollection Type ="Msi" EnforcementMode="NotConfigured" /> <RuleCollection Type ="Script" EnforcementMode="NotConfigured" /> <RuleCollection Type ="Dll" EnforcementMode="NotConfigured" /> <RuleCollection Type ="Appx" EnforcementMode="NotConfigured"> <FilePublisherRule Id="5e0c752b-5921-4f72-8146-80ad5f582110" Name="Microsoft.Windows.Photos, version 16.526.0.0 and above, from Microsoft Corporation" Description="" UserOrGroupSid="S-1-1-0" Action="Allow"> <Conditions> <FilePublisherCondition PublisherName="CN=Microsoft Corporation, O=Microsoft Corporation, L=Redmond, S=Washington, C=US" ProductName="Microsoft.Windows.Photos" BinaryName="*"> <BinaryVersionRange LowSection="16.526.0.0" HighSection="*" /> </FilePublisherCondition> </Conditions> </FilePublisherRule> </RuleCollection> </AppLockerPolicy> -
After you’ve created your XML file, you need to import it by using Microsoft Intune.
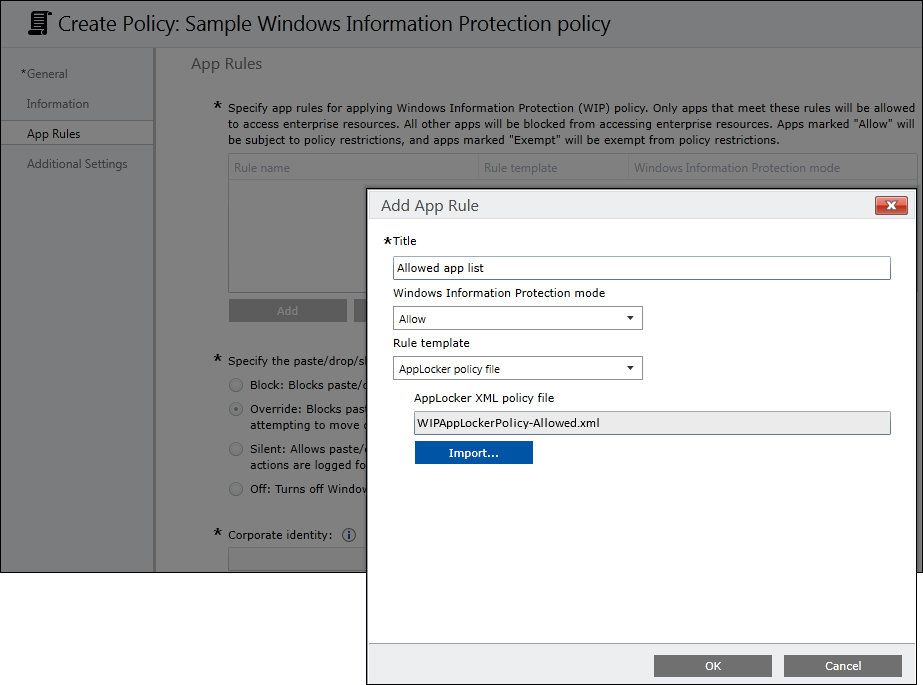
To import your Applocker policy file app rule using Microsoft Intune
-
From the App Rules area, click Add.
The Add App Rule box appears.
-
Add a friendly name for your app into the Title box. In this example, it’s Allowed app list.
-
Click Allow from the Windows Information Protection mode drop-down list.
Allow turns on WIP, helping to protect that app’s corporate data through the enforcement of WIP restrictions. Instructions for exempting an app are included in the Exempt apps from WIP restrictions section of this topic.
-
Pick AppLocker policy file from the Rule template drop-down list.
The box changes to let you import your AppLocker XML policy file.
-
Click Import, browse to your AppLocker XML file, click Open, and then click OK to close the Add App Rule box.
The file is imported and the apps are added to your App Rules list.
Exempt apps from WIP restrictions
If you're running into compatibility issues where your app is incompatible with WIP, but still needs to be used with enterprise data, you can exempt the app from the WIP restrictions. This means that your apps won't include auto-encryption or tagging and won't honor your network restrictions. It also means that your exempted apps might leak.
To exempt a store app, a desktop app, or an AppLocker policy file app rule
-
From the App Rules area, click Add.
The Add App Rule box appears.
-
Add a friendly name for your app into the Title box. In this example, it’s Exempt apps list.
-
Click Exempt from the Windows Information Protection mode drop-down list.
Be aware that when you exempt apps, they’re allowed to bypass the WIP restrictions and access your corporate data. To allow apps, see the Add app rules to your policy section of this topic.
-
Fill out the rest of the app rule info, based on the type of rule you’re adding:
-
Store app. Follow the Publisher and Product name instructions in the Add a store app rule to your policy section of this topic.
-
Desktop app. Follow the Publisher, Product name, Binary name, and Version instructions in the Add a desktop app rule to your policy section of this topic.
-
AppLocker policy file. Follow the Import instructions in the Add an AppLocker policy file section of this topic, using a list of exempted apps.
-
-
Click OK.
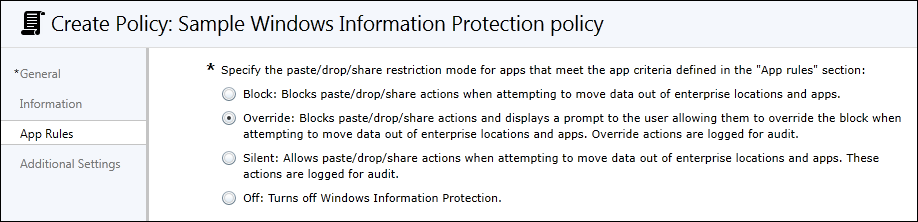
Manage the WIP protection mode for your enterprise data
After you've added the apps you want to protect with WIP, you'll need to apply a management and protection mode.
We recommend that you start with Silent or Override while verifying with a small group that you have the right apps on your protected apps list. After you're done, you can change to your final enforcement policy, either Override or Block.
| Mode | Description |
|---|---|
| Block | WIP looks for inappropriate data sharing practices and stops the employee from completing the action. This can include sharing info across non-enterprise-protected apps in addition to sharing enterprise data between other people and devices outside of your enterprise. |
| Override | WIP looks for inappropriate data sharing, warning employees if they do something deemed potentially unsafe. However, this management mode lets the employee override the policy and share the data, logging the action to your audit log, accessible through the Reporting CSP. |
| Silent | WIP runs silently, logging inappropriate data sharing, without blocking anything that would’ve been prompted for employee interaction while in Override mode. Unallowed actions, like apps inappropriately trying to access a network resource or WIP-protected data, are still blocked. |
| Off (not recommended) | WIP is turned off and doesn't help to protect or audit your data. After you turn off WIP, an attempt is made to decrypt any WIP-tagged files on the locally attached drives. Be aware that your previous decryption and policy info isn’t automatically reapplied if you turn WIP protection back on. |
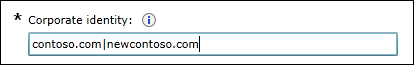
Define your enterprise-managed corporate identity
Corporate identity, usually expressed as your primary Internet domain (for example, contoso.com), helps to identify and tag your corporate data from apps you’ve marked as protected by WIP. For example, emails using contoso.com are identified as being corporate and are restricted by your Windows Information Protection policies.
You can specify multiple domains owned by your enterprise by separating them with the "|" character. For example, (contoso.com|newcontoso.com). With multiple domains, the first one is designated as your corporate identity and all of the additional ones as being owned by the first one. We strongly recommend that you include all of your email address domains in this list.
To add your corporate identity
-
Type the name of your corporate identity into the Corporate identity field. For example,
contoso.comorcontoso.com|newcontoso.com.
Choose where apps can access enterprise data
After you've added a protection mode to your apps, you'll need to decide where those apps can access enterprise data on your network.
There are no default locations included with WIP, you must add each of your network locations. This area applies to any network endpoint device that gets an IP address in your enterprise’s range and is also bound to one of your enterprise domains, including SMB shares. Local file system locations should just maintain encryption (for example, on local NTFS, FAT, ExFAT).
Important
Every WIP policy should include policy that defines your enterprise network locations.
Classless Inter-Domain Routing (CIDR) notation isn’t supported for WIP configurations.
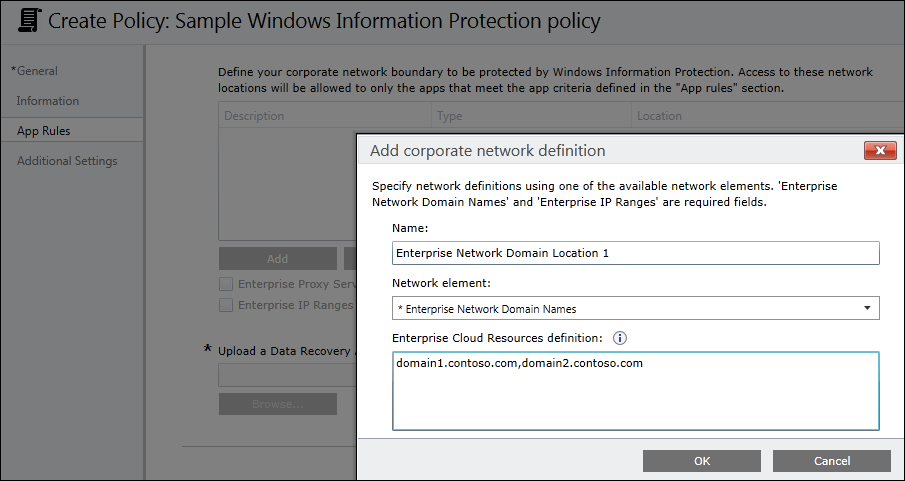
To define where your protected apps can find and send enterprise data on you network
-
Add additional network locations your apps can access by clicking Add.
The Add or edit corporate network definition box appears.
-
Type a name for your corporate network element into the Name box, and then pick what type of network element it is, from the Network element drop-down box. This can include any of the options in the following table.
| Network location type | Format | Description |
|---|---|---|
| Enterprise Cloud Resources | With proxy: contoso.sharepoint.com,contoso.internalproxy1.com| contoso.visualstudio.com,contoso.internalproxy2.com Without proxy: contoso.sharepoint.com|contoso.visualstudio.com |
Specify the cloud resources to be treated as corporate and protected by WIP. For each cloud resource, you may also optionally specify a proxy server from your Enterprise Internal Proxy Servers list to route traffic for this cloud resource. Be aware that all traffic routed through your Enterprise Internal Proxy Servers is considered enterprise. If you have multiple resources, you must separate them using the "|" delimiter. If you don’t use proxy servers, you must also include the "," delimiter just before the "|". For example: If Windows is unable to determine whether an app should be allowed to connect to a network resource, it will automatically block the connection. If instead you want Windows to allow the connections to happen, you can add the |
| Enterprise Network Domain Names (Required) | corp.contoso.com,region.contoso.com | Specify the DNS suffixes used in your environment. All traffic to the fully-qualified domains appearing in this list will be protected. This setting works with the IP ranges settings to detect whether a network endpoint is enterprise or personal on private networks. If you have multiple resources, you must separate them using the "," delimiter. |
| Enterprise Proxy Servers | proxy.contoso.com:80;proxy2.contoso.com:443 | Specify your externally-facing proxy server addresses, along with the port through which traffic accesses the Internet. This list must not include any servers listed in the Enterprise Internal Proxy Servers list, because they’re used for WIP-protected traffic. This setting is also required if there’s a chance you could end up behind a proxy server on another network. In this situation, if you don't have a proxy server pre-defined, you might find that enterprise resources are unavailable to your client device, such as when you’re visiting another company and not on the guest network. To make sure this doesn’t happen, the client device also needs to be able to reach the pre-defined proxy server through the VPN network. If you have multiple resources, you must separate them using the ";" delimiter. |
| Enterprise Internal Proxy Servers | contoso.internalproxy1.com;contoso.internalproxy2.com | Specify the proxy servers your devices will go through to reach your cloud resources. Using this server type indicates that the cloud resources you’re connecting to are enterprise resources. This list shouldn’t include any servers listed in the Enterprise Proxy Servers list, which are used for non-WIP-protected traffic. If you have multiple resources, you must separate them using the ";" delimiter. |
| Enterprise IPv4 Range (Required, if not using IPv6) | **Starting IPv4 Address:** 3.4.0.1 **Ending IPv4 Address:** 3.4.255.254 **Custom URI:** 3.4.0.1-3.4.255.254, 10.0.0.1-10.255.255.254 |
Specify the addresses for a valid IPv4 value range within your intranet. These addresses, used with your Enterprise Network Domain Names, define your corporate network boundaries. If you have multiple ranges, you must separate them using the "," delimiter. |
| Enterprise IPv6 Range (Required, if not using IPv4) | **Starting IPv6 Address:** 2a01:110:: **Ending IPv6 Address:** 2a01:110:7fff:ffff:ffff:ffff:ffff:ffff **Custom URI:** 2a01:110:7fff:ffff:ffff:ffff:ffff:ffff, fd00::-fdff:ffff:ffff:ffff:ffff:ffff:ffff:ffff |
Specify the addresses for a valid IPv6 value range within your intranet. These addresses, used with your Enterprise Network Domain Names, define your corporate network boundaries. If you have multiple ranges, you must separate them using the "," delimiter. |
| Neutral Resources | sts.contoso.com,sts.contoso2.com | Specify your authentication redirection endpoints for your company. These locations are considered enterprise or personal, based on the context of the connection before the redirection. If you have multiple resources, you must separate them using the "," delimiter. |
-
Add as many locations as you need, and then click OK.
The Add corporate network definition box closes.
-
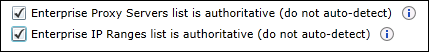
Decide if you want to Windows to look for additional network settings:
-
Enterprise Proxy Servers list is authoritative (do not auto-detect). Click this box if you want Windows to treat the proxy servers you specified in the network boundary definition as the complete list of proxy servers available on your network. If you clear this box, Windows will search for additional proxy servers in your immediate network.
-
Enterprise IP Ranges list is authoritative (do not auto-detect). Click this box if you want Windows to treat the IP ranges you specified in the network boundary definition as the complete list of IP ranges available on your network. If you clear this box, Windows will search for additional IP ranges on any domain-joined devices connected to your network.
-
-
In the required Upload a Data Recovery Agent (DRA) certificate to allow recovery of encrypted data box, click Browse to add a data recovery certificate for your policy.
After you create and deploy your WIP policy to your employees, Windows will begin to encrypt your corporate data on the employees’ local device drive. If somehow the employees’ local encryption keys get lost or revoked, the encrypted data can become unrecoverable. To help avoid this possibility, the DRA certificate lets Windows use an included public key to encrypt the local data, while you maintain the private key that can unencrypt the data.
For more info about how to find and export your data recovery certificate, see the Data Recovery and Encrypting File System (EFS) topic. For more info about creating and verifying your EFS DRA certificate, see the Create and verify an Encrypting File System (EFS) Data Recovery Agent (DRA) certificate.
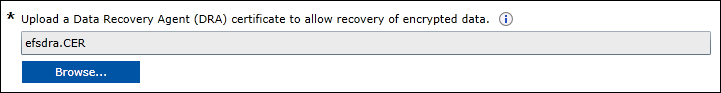
Choose your optional WIP-related settings
After you've decided where your protected apps can access enterprise data on your network, you’ll be asked to decide if you want to add any optional WIP settings.
To set your optional settings
-
Choose to set any or all of the optional settings:
-
Show the Personal option in the File ownership menus of File Explorer and the Save As dialog box. Determines whether users can see the Personal option for files within File Explorer and the Save As dialog box. The options are:
-
Yes, or not configured (recommended). Employees can choose whether a file is Work or Personal in File Explorer and the Save As dialog box.
-
No. Hides the Personal option from employees. Be aware that if you pick this option, apps that use the Save As dialog box might encrypt new files as corporate data unless a different file path is given during the original file creation. After this happens, decryption of work files becomes more difficult.
-
-
Prevent corporate data from being accessed by apps when the device is locked. Applies only to Windows 10 Mobile. Determines whether to encrypt enterprise data using a key that's protected by an employee's PIN code on a locked device. Apps won't be able to read corporate data when the device is locked. The options are:
-
Yes (recommended). Turns on the feature and provides the additional protection.
-
No, or not configured. Doesn't enable this feature.
-
-
Revoke encryption keys on unenroll. Determines whether to revoke a user’s local encryption keys from a device when it’s unenrolled from Windows Information Protection. If the encryption keys are revoked, a user no longer has access to encrypted corporate data. The options are:
-
Yes, or not configured (recommended). Revokes local encryption keys from a device during unenrollment.
-
No. Stop local encryption keys from being revoked from a device during unenrollment. For example, if you’re migrating between Mobile Device Management (MDM) solutions.
-
-
Allow Windows Search to search encrypted corporate data and Store apps. Determines whether Windows Search can search and index encrypted corporate data and Store apps. The options are:
-
Yes. Allows Windows Search to search and index encrypted corporate data and Store apps.
-
No, or not configured (recommended). Stops Windows Search from searching and indexing encrypted corporate data and Store apps.
-
-
Show the Windows Information Protection icon overlay. Determines whether the Windows Information Protection icon overlay appears on corporate files in the Save As and File Explorer views. The options are:
-
Yes. Allows the Windows Information Protection icon overlay to appear on corporate files in the Save As and File Explorer views. Additionally, for unenlightened but allowed apps, the icon overlay also appears on the app tile and with Managed text on the app name in the Start menu.
-
No, or not configured (recommended). Stops the Windows Information Protection icon overlay from appearing on corporate files or unenlightened, but allowed apps. Not configured is the default option.
-
-
-
Click Save Policy.
Note
Help to make this topic better by providing us with edits, additions, and feedback. For info about how to contribute to this topic, see Contributing to TechNet content.
Related topics
- Add apps to your Windows Information Protection (WIP) policy by using the Microsoft Intune custom URI functionality
- Deploy your Windows Information Protection (WIP) policy
- Create and deploy a VPN policy for Windows Information Protection (WIP) using Microsoft Intune
- General guidance and best practices for Windows Information Protection (WIP)