* Update windows/security/information-protection/windows-information-protection/testing-scenarios-for-wip.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * Update windows/security/threat-protection/windows-defender-exploit-guard/enable-controlled-folders-exploit-guard.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update policy-csp-update.md In 1903 we deprecated the value of 32 and combined Semi-Annual Channel (Targeted) with the Semi-Annual Channel. We need to communicate this change in the documentation. * chore: Replace tab after unorderd list marker * Update windows/security/identity-protection/credential-guard/credential-guard-manage.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * markdown syntex issue There was a syntex issue with formating. It has been fixed. * Update MDM Path https://docs.microsoft.com/en-us/windows/client-management/mdm/policy-csp-browser#browser-allowflash Issue https://github.com/MicrosoftDocs/windows-itpro-docs/issues/3553 * HTML Tag fix There was issue with HTML tag in live 203 and has been fixed. * Update windows/security/information-protection/windows-information-protection/testing-scenarios-for-wip.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/windows-defender-exploit-guard/enable-controlled-folders-exploit-guard.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-overview.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * Update waas-overview.md * Update hello-hybrid-cert-whfb-settings-policy.md removing extra "want" * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update hello-planning-guide.md * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * Update whiteboard-collaboration.md * Update hello-key-trust-policy-settings.md * Update integrate-configuration-manager-with-mdt.md * Update use-system-center-configuration-manager-to-manage-devices-with-semm.md * Update start-layout-xml-desktop.md Added syntax and note * remove reference about Windows 10 Pro https://github.com/MicrosoftDocs/windows-itpro-docs/issues/3255 * Fixed Typo * Adding Question to FAQ https://github.com/MicrosoftDocs/windows-itpro-docs/issues/4288 * Adding Question to FAQ https://github.com/MicrosoftDocs/windows-itpro-docs/issues/4288 * Updated with TVM refs * Emphasize Device Sync https://github.com/MicrosoftDocs/windows-itpro-docs/issues/4401 * Update windows/security/threat-protection/windows-defender-atp/configure-mssp-support.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/windows-defender-atp/configure-mssp-support.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * fix: MD005/list-indent Inconsistent indentation for list items at the same level * Update integrate-configuration-manager-with-mdt.md * Update use-system-center-configuration-manager-to-manage-devices-with-semm.md * Update enable-admx-backed-policies-in-mdm.md Added two links to notes. * Update windows/configuration/start-layout-xml-desktop.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update index.md Corrected typo: 'annd' to 'and' * Update windows/security/identity-protection/hello-for-business/hello-planning-guide.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update devices/surface-hub/whiteboard-collaboration.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/identity-protection/hello-for-business/hello-key-trust-policy-settings.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/identity-protection/hello-for-business/hello-key-trust-policy-settings.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/threat-protection/auditing/apply-a-basic-audit-policy-on-a-file-or-folder.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Create troubleshooting-agpm40-upgrades.md * Update TOC.md Addition of Troubleshooting AGPM Upgrades top-level link * Update windows-10-upgrade-paths.md * Update white-glove.md Removed a singular reference to WG and replaced with white glove * remove last 3 blocks in IT Admin * Fixes typo issue in line 47 Closes #4557 * Update metadata to replace non-existent author * Update index.md Typo - corrected 'Bitlocker' to 'BitLocker' * Rename windows/security/threat-protection/windows-defender-atp/configure-mssp-support.md to windows/security/threat-protection/microsoft-defender-atp/configure-mssp-support.md * Update hello-planning-guide.md * Update configure-wd-app-guard.md * Update configure-wd-app-guard.md * Update configure-wd-app-guard.md * Update kiosk-xml.md * Update kiosk-xml.md * Update waas-servicing-differences.md Removed double use of the word critical * Minor update to properly reflect supported macros * Update applocker-csp.md * Update kiosk-xml.md * Update applocker-csp.md * updated image needed I don't have rights to upload a new file (the updated error image) More details here: https://github.com/MicrosoftDocs/windows-itpro-docs/issues/2489 * MDOP May 2019 Servicing Release: new Hotfix Link Microsoft Desktop Optimization Pack May 2019 Servicing Release. Replaces the outdated MDOP link to July 2018 Servicing Release. Thanks to CaptainUnlikely for the Technet blogs information update. Closes #4574 * Creating a WDATP alert requires recommendedAction Otherwise the following will be returned by the API: ``` {"error":{"code":"BadRequest","message":"recommendedAction argument is missing"}} ``` * Update windows/security/threat-protection/windows-defender-application-guard/configure-wd-app-guard.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update guidelines-for-assigned-access-app.md * Corrected typo Changed "ConnecionSuccess" to "ConnectionSuccess * Update install-wd-app-guard.md * Update self-deploying.md Added additional links. * Update install-wd-app-guard.md * Update hello-hybrid-cert-trust-devreg.md * Update waas-delivery-optimization.md fixed typo * Fixed a small typo Changed "wwitches" to "switches". * Update for the month June 2019 I have added the content for surface hub based on an update KB4503289. There was no update released for a hub for the month of July. Problem: https://github.com/MicrosoftDocs/windows-itpro-docs/issues/4586 * Update devices/surface-hub/surface-hub-update-history.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * typo typo the Action Sataus column instead of the Action Status column * Correcting small mistake on which version of Win10 displays MBEC Correcting initial mistake when changed docs. * Updated links Hotlink for configuring MTP integration and API support was missing and has been updated. Problem: https://github.com/MicrosoftDocs/windows-itpro-docs/issues/4569 * Resolves #4620 - typo in command line Issue #4620 Set-ProcesMitigation -Name c:\apps\lob\tests\testing.exe -Enable AuditDynamicCode should be Set-ProcessMitigation -Name c:\apps\lob\tests\testing.exe -Enable AuditDynamicCode * HTML to MarkDown in hello-hybrid-aadj-sso-cert.md This is a combined effort to alleviate a translation bug as well as improving the MarkDown codestyle in this document, both for the English (en-us) version of the document as well as the translated versions. This change should in theory close the issue tickets #3451 and #3453 after the scripted translation process has been re-run on this document. This solution is based on a user discussion in issue ticket #4589 . * Update windows/deployment/windows-autopilot/self-deploying.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update index.md * Update waas-configure-wufb.md * Update hello-features.md Removes \ typo * Update windows-analytics-get-started.md adding IE site discovery to GDPR blurb * Update sideload-apps-in-windows-10.md * Update upgrade-readiness-deployment-script.md replacing support email with official support channels * missing bold on GUI element * formatting again - italicize typed word * fixing warnings * restored missing art, somehow * CAT Auto Pulish for Windows Release Messages - CAT_AutoPublish_2019080917545405 (#881)
11 KiB
title, ms.assetid, ms.reviewer, manager, ms.author, description, keywords, ms.prod, ms.mktglfcycl, ms.localizationpriority, ms.sitesec, ms.pagetype, audience, author, ms.topic
| title | ms.assetid | ms.reviewer | manager | ms.author | description | keywords | ms.prod | ms.mktglfcycl | ms.localizationpriority | ms.sitesec | ms.pagetype | audience | author | ms.topic |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Set up MDT for BitLocker (Windows 10) | 386e6713-5c20-4d2a-a220-a38d94671a38 | laurawi | greglin | disk, encryption, TPM, configure, secure, script | w10 | deploy | medium | library | mdt | itpro | greg-lindsay | article |
Set up MDT for BitLocker
This topic will show you how to configure your environment for BitLocker, the disk volume encryption built into Windows 10 Enterprise and Windows 10 Pro, using MDT. BitLocker in Windows 10 has two requirements in regard to an operating system deployment:
- A protector, which can either be stored in the Trusted Platform Module (TPM) chip, or stored as a password. Technically, you also can use a USB stick to store the protector, but it's not a practical approach as the USB stick can be lost or stolen. We, therefore, recommend that you instead use a TPM chip and/or a password.
- Multiple partitions on the hard drive.
To configure your environment for BitLocker, you will need to do the following:
- Configure Active Directory for BitLocker.
- Download the various BitLocker scripts and tools.
- Configure the operating system deployment task sequence for BitLocker.
- Configure the rules (CustomSettings.ini) for BitLocker.
Note
Even though it is not a BitLocker requirement, we recommend configuring BitLocker to store the recovery key and TPM owner information in Active Directory. For additional information about these features, see Backing Up BitLocker and TPM Recovery Information to AD DS. If you have access to Microsoft BitLocker Administration and Monitoring (MBAM), which is part of Microsoft Desktop Optimization Pack (MDOP), you have additional management features for BitLocker.
For the purposes of this topic, we will use DC01, a domain controller that is a member of the domain contoso.com for the fictitious Contoso Corporation. For more details on the setup for this topic, please see Deploy Windows 10 with the Microsoft Deployment Toolkit.
Configure Active Directory for BitLocker
To enable BitLocker to store the recovery key and TPM information in Active Directory, you need to create a Group Policy for it in Active Directory. For this section, we are running Windows Server 2012 R2, so you do not need to extend the Schema. You do, however, need to set the appropriate permissions in Active Directory.
Note
Depending on the Active Directory Schema version, you might need to update the Schema before you can store BitLocker information in Active Directory.
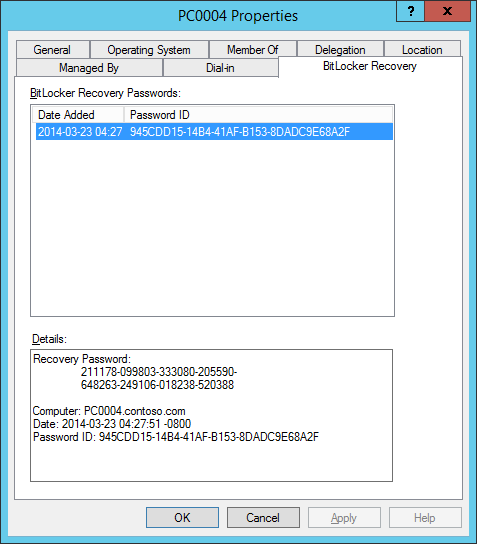
In Windows Server 2012 R2 (as well as in Windows Server 2008 R2 and Windows Server 2012), you have access to the BitLocker Drive Encryption Administration Utilities features, which will help you manage BitLocker. When you install the features, the BitLocker Active Directory Recovery Password Viewer is included, and it extends Active Directory Users and Computers with BitLocker Recovery information.
Figure 2. The BitLocker Recovery information on a computer object in the contoso.com domain.
Add the BitLocker Drive Encryption Administration Utilities
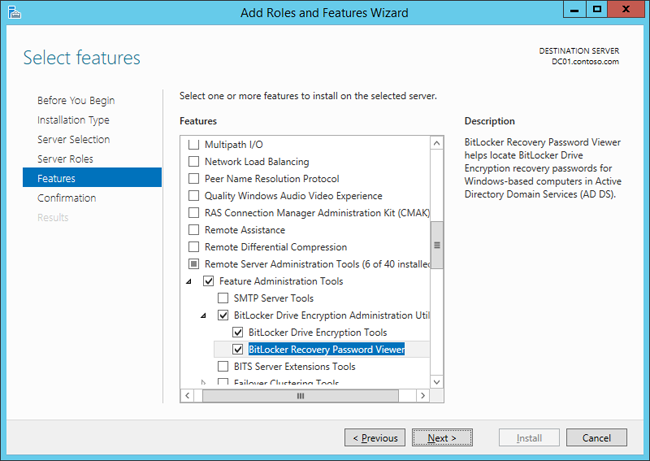
The BitLocker Drive Encryption Administration Utilities are added as features via Server Manager (or Windows PowerShell):
- On DC01, log on as CONTOSO\Administrator, and, using Server Manager, click Add roles and features.
- On the Before you begin page, click Next.
- On the Select installation type page, select Role-based or feature-based installation, and click Next.
- On the Select destination server page, select DC01.contoso.com and click Next.
- On the Select server roles page, click Next.
- On the Select features page, expand Remote Server Administration Tools, expand Feature Administration Tools, select the following features, and then click Next:
- BitLocker Drive Encryption Administration Utilities
- BitLocker Drive Encryption Tools
- BitLocker Recovery Password Viewer
- On the Confirm installation selections page, click Install and then click Close.
Figure 3. Selecting the BitLocker Drive Encryption Administration Utilities.
Create the BitLocker Group Policy
Following these steps, you enable the backup of BitLocker and TPM recovery information to Active Directory. You also enable the policy for the TPM validation profile.
- On DC01, using Group Policy Management, right-click the Contoso organizational unit (OU), and select Create a GPO in this domain, and Link it here.
- Assign the name BitLocker Policy to the new Group Policy.
- Expand the Contoso OU, right-click the BitLocker Policy, and select Edit. Configure the following policy settings:
Computer Configuration / Policies / Administrative Templates / Windows Components / BitLocker Drive Encryption / Operating System Drives
- Enable the Choose how BitLocker-protected operating system drives can be recovered policy, and configure the following settings:
- Allow data recovery agent (default)
- Save BitLocker recovery information to Active Directory Domain Services (default)
- Do not enable BitLocker until recovery information is stored in AD DS for operating system drives
- Enable the Configure TPM platform validation profile for BIOS-based firmware configurations policy.
- Enable the Configure TPM platform validation profile for native UEFI firmware configurations policy. Computer Configuration / Policies / Administrative Templates / System / Trusted Platform Module Services
- Enable the Turn on TPM backup to Active Directory Domain Services policy.
- Enable the Choose how BitLocker-protected operating system drives can be recovered policy, and configure the following settings:
Note
If you consistently get the error "Windows BitLocker Drive Encryption Information. The system boot information has changed since BitLocker was enabled. You must supply a BitLocker recovery password to start this system." after encrypting a computer with BitLocker, you might have to change the various "Configure TPM platform validation profile" Group Policies, as well. Whether or not you need to do this will depend on the hardware you are using.
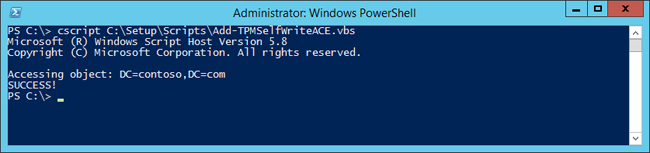
Set permissions in Active Directory for BitLocker
In addition to the Group Policy created previously, you need to configure permissions in Active Directory to be able to store the TPM recovery information. In these steps, we assume you have downloaded the Add-TPMSelfWriteACE.vbs script from Microsoft to C:\Setup\Scripts on DC01.
-
On DC01, start an elevated PowerShell prompt (run as Administrator).
-
Configure the permissions by running the following command:
cscript C:\Setup\Scripts\Add-TPMSelfWriteACE.vbs
Figure 4. Running the Add-TPMSelfWriteACE.vbs script on DC01.
Add BIOS configuration tools from Dell, HP, and Lenovo
If you want to automate enabling the TPM chip as part of the deployment process, you need to download the vendor tools and add them to your task sequences, either directly or in a script wrapper.
Add tools from Dell
The Dell tools are available via the Dell Client Configuration Toolkit (CCTK). The executable file from Dell is named cctk.exe. Here is a sample command to enable TPM and set a BIOS password using the cctk.exe tool:
cctk.exe --tpm=on --valsetuppwd=Password1234
Add tools from HP
The HP tools are part of HP System Software Manager. The executable file from HP is named BiosConfigUtility.exe. This utility uses a configuration file for the BIOS settings. Here is a sample command to enable TPM and set a BIOS password using the BiosConfigUtility.exe tool:
BIOSConfigUtility.EXE /SetConfig:TPMEnable.REPSET /NewAdminPassword:Password1234
And the sample content of the TPMEnable.REPSET file:
English
Activate Embedded Security On Next Boot
*Enable
Embedded Security Activation Policy
*No prompts
F1 to Boot
Allow user to reject
Embedded Security Device Availability
*Available
Add tools from Lenovo
The Lenovo tools are a set of VBScripts available as part of the Lenovo BIOS Setup using Windows Management Instrumentation Deployment Guide. Lenovo also provides a separate download of the scripts. Here is a sample command to enable TPM using the Lenovo tools:
cscript.exe SetConfig.vbs SecurityChip Active
Configure the Windows 10 task sequence to enable BitLocker
When configuring a task sequence to run any BitLocker tool, either directly or using a custom script, it is helpful if you also add some logic to detect whether the BIOS is already configured on the machine. In the following task sequence, we are using a sample script (ZTICheckforTPM.wsf) from the Deployment Guys web page to check the status on the TPM chip. You can download this script from the Deployment Guys Blog post, Check to see if the TPM is enabled.
In the following task sequence, we added five actions:
-
Check TPM Status. Runs the ZTICheckforTPM.wsf script to determine if TPM is enabled. Depending on the status, the script will set the TPMEnabled and TPMActivated properties to either true or false.
-
Configure BIOS for TPM. Runs the vendor tools (in this case, HP, Dell, and Lenovo). To ensure this action is run only when necessary, add a condition so the action is run only when the TPM chip is not already activated. Use the properties from the ZTICheckforTPM.wsf. Note It is common for organizations to wrap these tools in scripts to get additional logging and error handling.
-
Restart computer. Self-explanatory, reboots the computer.
-
Check TPM Status. Runs the ZTICheckforTPM.wsf script one more time.
-
Enable BitLocker. Runs the built-in action to activate BitLocker.
Related topics
Configure MDT deployment share rules
Configure MDT for UserExit scripts
Simulate a Windows 10 deployment in a test environment
Use the MDT database to stage Windows 10 deployment information