5.1 KiB
title, description, keywords, search.product, ms.pagetype, ms.prod, ms.mktglfcycl, ms.sitesec, ms.pagetype, localizationpriority, author, ms.author
| title | description | keywords | search.product | ms.pagetype | ms.prod | ms.mktglfcycl | ms.sitesec | ms.pagetype | localizationpriority | author | ms.author |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Enable ASR rules individually to protect your organization | Enable ASR rules to protect your devices from attacks the use macros, scripts, and common injection techniques | Attack Surface Reduction, hips, host intrusion prevention system, protection rules, anti-exploit, antiexploit, exploit, infection prevention, enable, turn on | eADQiWindows 10XVcnh | security | w10 | manage | library | security | medium | iaanw | iawilt |
Enable Attack Surface Reduction
Applies to:
- Windows 10 Insider Preview
Audience
- Enterprise security administrators
Manageability available with
- Group Policy
- PowerShell
- Configuration service providers for mobile device management
Attack Surface Reduction is a feature that is part of Windows Defender Exploit Guard. It helps prevent actions and apps that are typically used by exploit-seeking malware to infect machines.
Enable and audit Attack Surface Reduction rules
You can use Group Policy, PowerShell, or MDM CSPs to configure the state or mode for each rule. This can be useful if you only want to enable some rules, or you want to enable rules individually in audit mode.
For further details on how audit mode works, and when you might want to use it, see the audit Windows Defender Exploit Guard topic.
Attack Surface Reduction rules are identified by their unique rule ID.
Rule IDs willl be populated on machines that are enrolled in an E5 license. These machines will also properly report their Attack Surface Reduction rule history in the Windows Defender Security Center web console.
You can also manually add the rules from the following table:
| Rule description | GUIDs |
|---|---|
| Block executable content from email client and webmail. | be9ba2d9-53ea-4cdc-84e5-9b1eeee46550 |
| Block Office applications from creating child processes | {d4f940ab-401b-4efc-aadc-ad5f3c50688a} |
| Block Office applications from creating executable content | {3b576869-a4ec-4529-8536-b80a7769e899} |
| Block Office applications from injecting into other processes | {75668c1f-73b5-4cf0-bb93-3ecf5cb7cc84} |
| Impede JavaScript and VBScript to launch executables | {d3e037e1-3eb8-44c8-a917-57927947596d} |
| Block execution of potentially obfuscated scripts | {5beb7efe-fd9a-4556-801d-275e5ffc04cc} |
Block Win32 imports from Macro code in Office | {92E97FA1-2EDF-4476-BDD6-9DD0B4DDDC7B}
Note
I don't see this rule in the test tool
See the Evaluate Attack Surface Reduction rules topic for details on each rule.
Note
Are we revealing the rule GUIDs? Will they appear on E5 machines?
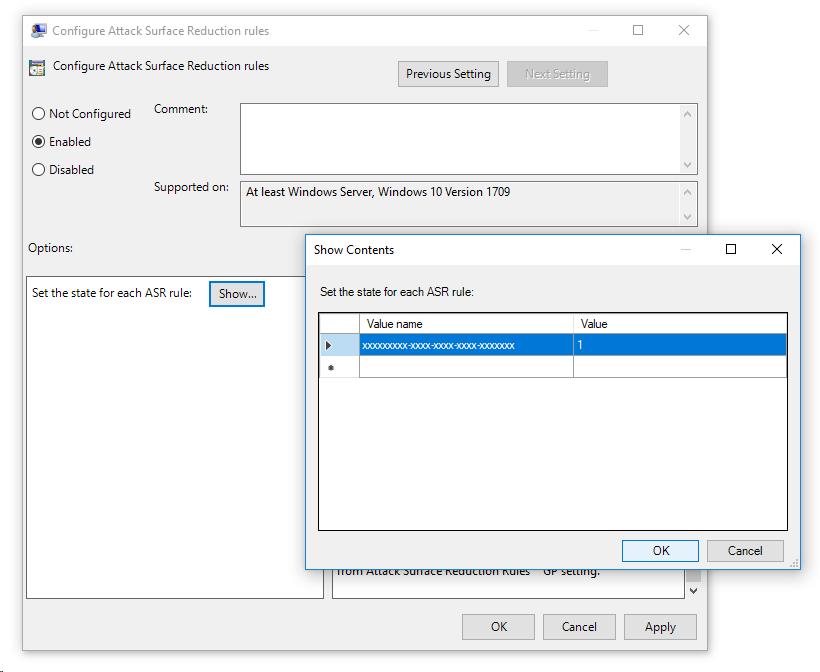
Use Group Policy to enable Attack Surface Reduction rules
-
On your Group Policy management machine, open the Group Policy Management Console, right-click the Group Policy Object you want to configure and click Edit.
-
In the Group Policy Management Editor go to Computer configuration.
-
Click Policies then Administrative templates.
-
Expand the tree to Windows components > Windows Defender Antivirus > Windows Defender Exploit Guard > Attack Surface Reduction.
-
Double-click the Configure Attack Surface Reduction rules setting and set the option to Enabled. You can then set the individual state for each rule in the options section:
Use PowerShell to enable Attack Surface Reduction rules
-
Type powershell in the Start menu, right click Windows PowerShell and click Run as administrator
-
Enter the following cmdlet:
Add-MpPreference -AttackSurfaceReductionRules_Ids <rule ID>
Note
Not sure if this is right. What does AttackSurfaceReductionRules_Actions do? Do you need to add $TRUE/$FALSE or 1/0 at the end to enable it? Does the rule need to go in " or {}? Some examples would be handy here I think
You can enable the feauting in audit mode using the following cmdlet:
Set-MpPreference -AttackSurfaceReductionRules_Actions AuditMode
Use Disabled insead of AuditMode or Enabled to turn the feature off.
Note
We need to walk through this so I understand how it works
Use MDM CSPs to enable Attack Surface Reduction rules
Use the ./Vendor/MSFT/Policy/Config/Defender/AttackSurfaceReductionRules configuration service provider (CSP) to individually enable and set the mode for each rule.