12 KiB
title, description, ms.author, ms.topic, ms.prod, ms.technology, author, ms.date
| title | description | ms.author | ms.topic | ms.prod | ms.technology | author | ms.date |
|---|---|---|---|---|---|---|---|
| ApplicationControl CSP | ApplicationControl CSP | dansimp | article | w10 | windows | ManikaDhiman | 05/21/2019 |
ApplicationControl CSP
Windows Defender Application Control (WDAC) policies can be managed from an MDM server through ApplicationControl configuration service provider (CSP). This CSP provides expanded diagnostic capabilities and support for multiple policies (introduced in Windows 10, version 1903). It also provides support for rebootless policy deployment (introduced in Windows 10, version 1709). Unlike AppLocker CSP, ApplicationControl CSP correctly detects the presence of no-reboot option and consequently does not schedule a reboot. Existing WDAC policies deployed using AppLocker CSP’s CodeIntegrity node can now be deployed using ApplicationControl CSP URI. Although WDAC policy deployment via AppLocker CSP will continue to be supported, all new feature work will be done in ApplicationControl CSP only.
ApplicationControl CSP was added in Windows 10, version 1903.
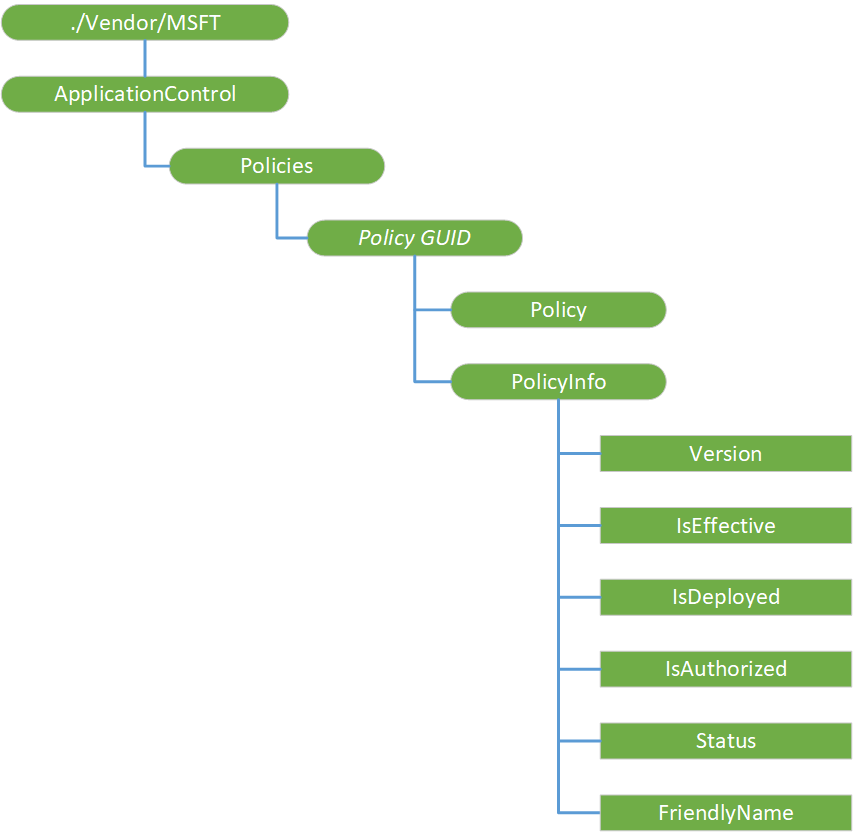
The following diagram shows ApplicationControl CSP in tree format.
./Vendor/MSFT/ApplicationControl
Defines the root node for ApplicationControl CSP.
Scope is permanent. Supported operation is Get.
ApplicationControl/Policies
An interior node that contains all the policies, each identified by their globally unique identifier (GUID).
Scope is permanent. Supported operation is Get.
ApplicationControl/Policies/Policy GUID
ApplicationControl CSP enforces that the “ID” segment of a given policy URI is the same GUID as the policy ID in the policy blob. Each Policy GUID node contains a Policy node and a corresponding PolicyInfo node.
Scope is dynamic. Supported operation is Get.
ApplicationControl/Policies/Policy GUID/Policy
This node is the policy binary itself, which is encoded as base64.
Scope is dynamic. Supported operations are Get, Add, Delete, and Replace.
Value type is b64. Supported value is any well-formed WDAC policy, i.e. the base64-encoded content output by the ConvertFrom-CIPolicy cmdlet.
Default value is empty.
ApplicationControl/Policies/Policy GUID/PolicyInfo
An interior node that contains the nodes that describe the policy indicated by the GUID.
Scope is dynamic. Supported operation is Get.
ApplicationControl/Policies/Policy GUID/PolicyInfo/Version
This node provides the version of the policy indicated by the GUID. Stored as a string, but when parsing use a uint64 as the containing data type.
Scope is dynamic. Supported operation is Get.
Value type is char.
ApplicationControl/Policies/Policy GUID/PolicyInfo/IsEffective
This node specifies whether a policy is actually loaded by the enforcement engine and is in effect on a system.
Scope is dynamic. Supported operation is Get.
Value type is bool. Supported values are as follows:
- True — Indicates that the policy is actually loaded by the enforcement engine and is in effect on a system.
- False — Indicates that the policy is not loaded by the enforcement engine and is not in effect on a system. This is the default.
ApplicationControl/Policies/Policy GUID/PolicyInfo/IsDeployed
This node specifies whether a policy is deployed on the system and is present on the physical machine.
Scope is dynamic. Supported operation is Get.
Value type is bool. Supported values are as follows:
- True — Indicates that the policy is deployed on the system and is present on the physical machine.
- False — Indicates that the policy is not deployed on the system and is not present on the physical machine. This is the default.
ApplicationControl/Policies/Policy GUID/PolicyInfo/IsAuthorized
This node specifies whether the policy is authorized to be loaded by the enforcement engine on the system. If not authorized, a policy cannot take effect on the system.
Scope is dynamic. Supported operation is Get.
Value type is bool. Supported values are as follows:
- True — Indicates that the policy is authorized to be loaded by the enforcement engine on the system.
- False — Indicates that the policy is not authorized to be loaded by the enforcement engine on the system. This is the default.
The following table provides the result of this policy based on different values of IsAuthorized, IsDeployed, and IsEffective nodes:
| IsAuthorized | IsDeployed | IsEffective | Resultant |
|---|---|---|---|
| True | True | True | Policy is currently running and in effect. |
| True | True | False | Policy requires a reboot to take effect. |
| True | False | True | Policy requires a reboot to unload from CI. |
| False | True | True | Not Reachable. |
| True | False | False | *Not Reachable. |
| False | True | False | *Not Reachable. |
| False | False | True | Not Reachable. |
| False | False | False | *Not Reachable. |
* denotes a valid intermediary state; however, if an MDM transaction results in this state configuration, the END_COMMAND_PROCESSING will result in a fail.
ApplicationControl/Policies/Policy GUID/PolicyInfo/Status
This node specifies whether the deployment of the policy indicated by the GUID was successful.
Scope is dynamic. Supported operation is Get.
Value type is integer. Default value is 0 == OK.
ApplicationControl/Policies/Policy GUID/PolicyInfo/FriendlyName
This node provides the friendly name of the policy indicated by the policy GUID.
Scope is dynamic. Supported operation is Get.
Value type is char.
Usage Guidance
![Note] If using Intune standalone or for hybrid management with Configuration Manager (SCCM) through Microsoft Endpoint Manager, refer to Deploy Windows Defender Application Control policies by using Microsoft Intune for more information on deploying policies with ApplicationControl CSP. Microsoft Intune handles the creation of a policy node and does all the below steps to deploy policies on your behalf, so you shouldn't do any of the below steps if using Intune to leverage ApplicationControl CSP.
In order to use ApplicationControl CSP, you must:
- Know a generated policy’s GUID, which can be found in the policy xml as
<PolicyID>or<PolicyTypeID>for pre-1903 systems. - Convert the policies to binary format using the ConvertFrom-CIPolicy cmdlet in order to be deployed. The binary policy may be signed or unsigned.
- Create a policy node (a Base64-encoded blob of the binary policy representation) using the certutil -encode command line tool.
Here is a sample certutil invocation:
certutil -encode WinSiPolicy.p7b WinSiPolicy.cer
An alternative to using certutil would be to use the following PowerShell invocation:
[Convert]::toBase64String($(Get-Content -Encoding Byte -ReadCount 0 -Path <bin file>))
Deploy policies
In order to deploy a new base policy or supplemental policy using the CSP:
- Perform an ADD on ./Vendor/MSFT/ApplicationControl/Policies/{Policy GUID}/Policy using the Base64-encoded policy node as {Data} with the GUID and policy data for the base policy. Refer to the the Format section in the Example 1 below.
- Repeat for each base or supplemental policy (with its own GUID and data).
The following example shows the deployment of two base policies and a supplemental policy. Because the supplemental policy already specifies the base policy it supplements, that does not need to be repeated in the ADD.
Example 1: Add first base policy
<Add>
<CmdID>1</CmdID>
<Item>
<Target>
<LocURI>./Vendor/MSFT/ApplicationControl/Policies/{Base1GUID}/Policy</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">b64</Format>
</Meta>
<Data> {Base1Data} </Data>
</Item>
</Add>
Example 2: Add second base policy
<Add>
<CmdID>1</CmdID>
<Item>
<Target>
<LocURI>./Vendor/MSFT/ApplicationControl/Policies/{Base2GUID}/Policy</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">b64</Format>
</Meta>
<Data> {Base2Data} </Data>
</Item>
</Add>
Example 3: Add supplemental policy
<Add>
<CmdID>1</CmdID>
<Item>
<Target>
<LocURI>./Vendor/MSFT/ApplicationControl/Policies/{Supplemental1GUID}/Policy</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">b64</Format>
</Meta>
<Data> {Supplemental1Data} </Data>
</Item>
</Add>
Get policies
Perform a GET using a deployed policy’s GUID to interrogate/inspect the policy itself or information about it.
The following table displays the result of Get operation on different nodes:
| Nodes | Get Results |
|---|---|
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/Policy | raw p7b |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/Version | Policy version |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/IsEffective | Is the policy in effect |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/IsDeployed | Is the policy on the system |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/IsAuthorized | Is the policy authorized on the system |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/Status | Was the deployment successful |
| ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/PolicyInfo/FriendlyName | Friendly name per the policy |
The following is an example of Get command:
<Get>
<CmdID>1</CmdID>
<Item>
<Target>
<LocURI>./Vendor/MSFT/ApplicationControl/Policies/{PolicyGUID}/Policy</LocURI>
</Target>
</Item>
</Get>
Delete policies
To delete an unsigned policy, perform a DELETE on ./Vendor/MSFT/ApplicationControl/Policies/{Policy GUID}/Policy.
Only signed things should be able to update signed policies. Hence, performing a DELETE on ./Vendor/MSFT/ApplicationControl/Policies/{Policy GUID}/Policy is not sufficient to delete a signed policy.
To delete a signed policy:
- Replace it with a signed update allowing unsigned policy.
- Deploy another update with unsigned policy.
- Perform delete.
The following is an example of Delete command:
<Delete>
<CmdID>1</CmdID>
<Item>
<Target>
<LocURI>./Vendor/MSFT/ApplicationControl/Policies/{PolicyGUID}/Policy</LocURI>
</Target>
</Item>
</Delete>