* Updated deployment-vdi-windows-defender-antivirus.md * Updated deployment-vdi-windows-defender-antivirus.md * Updated deployment-vdi-windows-defender-antivirus.md * updates for new vdi stuff * Adding important note to solve #3493 * Update windows/security/identity-protection/hello-for-business/hello-hybrid-key-whfb-settings-dir-sync.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Typo "<"→"<", ">"→">" https://docs.microsoft.com/en-us/windows/application-management/manage-windows-mixed-reality * Issue #2297 * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Clarification * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * update troubleshoot-np.md * update configure-endpoints-gp.md * Removing a part which is not supported * Name change * update troubleshoot-np.md * removed on-premises added -hello * Added link into Domain controller guide * Line corections * corrected formatting of xml code samples When viewing the page in Win 10/Edge, the xml code samples stretched across the page, running into the side menu. The lack of line breaks also made it hard to read. This update adds line breaks and syntax highlighting, replaces curly double quotes with standard double quotes, and adds a closing tag for <appv:appconnectiongroup>for each code sample * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * corrected formating of XML examples The XML samples here present the same formatting problems as in about-the-connection-group-file51.md (see https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3847/) Perhaps we should open an issue to see if we have more versions of this code sample in the docs * corrected formatting of XML example section In the XML example on this page, the whitespace had been stripped out, so there were no spaces between adjacent attribute values or keys. This made it hard to read, though the original formatting allowed for a scroll bar, so the text was not running into the side of the page (compare to https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3847 and https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3850, where the uncorrected formatting forced the text to run into the side menu). * update configure-endpoints-gp.md * Fixed error in registry path and improved description * Update windows/security/identity-protection/hello-for-business/hello-hybrid-key-whfb-settings-dir-sync.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * Removing extra line in 25 Suggested by * update windows-analytics-azure-portal.md * re: broken links, credential-guard-considerations Context: * #3513, MVA is being retired and producing broken links * #3860 Microsoft Virtual Academy video links This page contains two links to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course the two links point to is already retired, and no replacement course exists. I removed the first link, as I could not find a similar video available describing which credentials are covered by credential guard. I replaced the second link with a video containing similar material, though it is not a "deep dive". Suggestions on handling this problem, as many pages contain similar links, would be appreciated,. * removed link to retired video re: #3867 Context: * #3513, MVA is being retired and producing broken links * #3867, Microsoft Virtual Academy video links This page contains a broken link to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course is already retired, and no replacement course exists. I removed the whole _See Also_ section, as I could not find a video narrowly or deeply addressing how to protect privelaged users with Credential Guard. The most likely candidate is too short and general: https://www.linkedin.com/learning/cism-cert-prep-1-information-security-governance/privileged-account-management * addressing broken mva links, #3817 Context: * #3513, MVA is being retired and producing broken links * #3817, Another broken link This page contains two links to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course the two links point to is already retired, and no replacement course exists. I removed the first link, as we no longer have a video with similar content for a similar audience. The most likely candidate is https://www.linkedin.com/learning/programming-foundations-web-security-2/types-of-credential-attacks, which is more general and for a less technical audience. I removed the second link and the _See Also_ section, as I could not find a similar video narrowly focused on which credentials are covered by Credential Guard. Most of the related material available now describes how to perform a task. * Update deployment-vdi-windows-defender-antivirus.md * typo fix re: #3876; DMSA -> DSMA * Addressing dead MVA links, #3818 This page, like its fellows in the mva-links label, contains links to a retired video course on a website that is retiring soon. The links listed by the user in issue #3818 were also on several other pages, related to Credentials Guard. These links were addressed in the pull requests #3875, #3872, and #3871 Credentials threat & lateral threat link: removed (see PR #3875 for reasoning) Virtualization link: replaced (see #3871 for reasoning) Credentials protected link: removed (see #3872 for reasoning) * Adding notes for known issue in script Solves #3869 * Updated the download link admx files Windows 10 Added link for April 2018 and Oct 2018 ADMX files. * added event logs path Referenced : https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-defender-exploit-guard/event-views-exploit-guard * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Suggestions applied. Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update deployment-vdi-windows-defender-antivirus.md * screenshot update * Add files via upload * update 4 scrrenshots * Update deployment-vdi-windows-defender-antivirus.md * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Re: #3909 Top link is broken, #3909 > The link here does not work: > Applies to: Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP) The link to the pdf describing MDATP was broken. Thankfully, PR #2897 updated the same link in another page some time ago, so I didn't have to go hunting for an equivalent * CI Update * Updated as per task 3405344 * Updated author * Update windows-analytics-azure-portal.md * added the example query * Updated author fields * Update office-csp.md * update video for testing * update video * Update surface-hub-site-readiness-guide.md line 134 Fixed video link MD formatting * fixing video url * updates from Albert * Bulk replaced author to manikadhiman * Bulk replaced ms.author to v-madhi * Latest content is published (#371) * Added 1903 policy DDF link and fixed a typo * Reverted the DDF version * Latest update (#375) * Update deployment-vdi-windows-defender-antivirus.md * Update deployment-vdi-windows-defender-antivirus.md
9.7 KiB
title, description, ms.pagetype, ms.prod, ms.mktglfcycl, ms.sitesec, ms.localizationpriority, author, ms.date, ms.reviewer, manager, ms.author
| title | description | ms.pagetype | ms.prod | ms.mktglfcycl | ms.sitesec | ms.localizationpriority | author | ms.date | ms.reviewer | manager | ms.author |
|---|---|---|---|---|---|---|---|---|---|---|---|
| 5137(S) A directory service object was created. (Windows 10) | Describes security event 5137(S) A directory service object was created. | security | w10 | deploy | library | none | dansimp | 04/19/2017 | dansimp | dansimp |
5137(S): A directory service object was created.
Applies to
- Windows 10
- Windows Server 2016
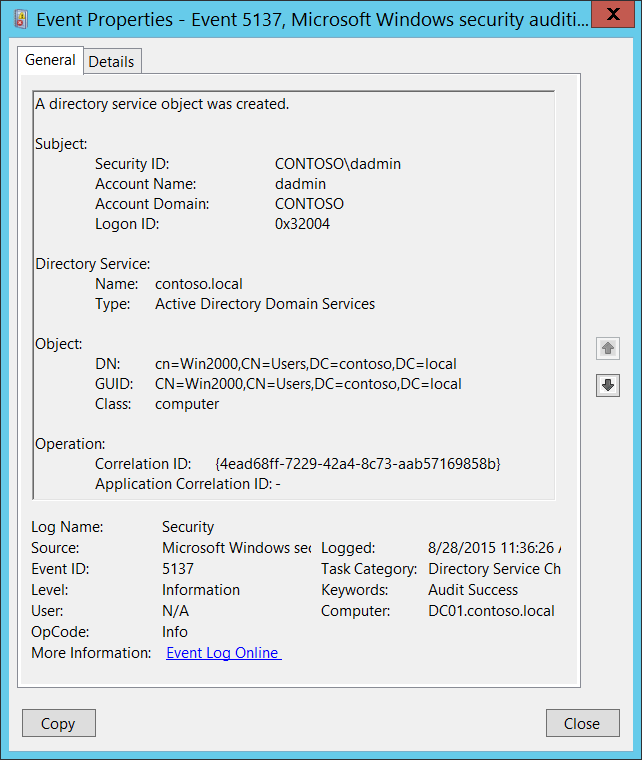
Subcategory: Audit Directory Service Changes
Event Description:
This event generates every time an Active Directory object is created.
This event only generates if the parent object has a particular entry in its SACL: the “Create” action, auditing for specific classes or objects. An example is the “Create Computer objects” action auditing for the organizational unit.
Note
For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>5137</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>14081</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2015-08-28T18:36:26.048167500Z" />
<EventRecordID>410737</EventRecordID>
<Correlation />
<Execution ProcessID="516" ThreadID="3156" />
<Channel>Security</Channel>
<Computer>DC01.contoso.local</Computer>
<Security />
</System>
- <EventData>
<Data Name="OpCorrelationID">{4EAD68FF-7229-42A4-8C73-AAB57169858B}</Data>
<Data Name="AppCorrelationID">-</Data>
<Data Name="SubjectUserSid">S-1-5-21-3457937927-2839227994-823803824-1104</Data>
<Data Name="SubjectUserName">dadmin</Data>
<Data Name="SubjectDomainName">CONTOSO</Data>
<Data Name="SubjectLogonId">0x32004</Data>
<Data Name="DSName">contoso.local</Data>
<Data Name="DSType">%%14676</Data>
<Data Name="ObjectDN">cn=Win2000,CN=Users,DC=contoso,DC=local</Data>
<Data Name="ObjectGUID">{41D5F7AF-64A2-4985-9A4B-70DAAFC7CCE6}</Data>
<Data Name="ObjectClass">computer</Data>
</EventData>
</Event>
Required Server Roles: Active Directory domain controller.
Minimum OS Version: Windows Server 2008.
Event Versions: 0.
Field Descriptions:
Subject:
- Security ID [Type = SID]: SID of account that requested the “create object” operation. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Note
A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
-
Account Name [Type = UnicodeString]: the name of the account that requested the “create object” operation.
-
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
-
Domain NETBIOS name example: CONTOSO
-
Lowercase full domain name: contoso.local
-
Uppercase full domain name: CONTOSO.LOCAL
-
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
-
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
-
-
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Directory Service:
-
Name [Type = UnicodeString]: the name of an Active Directory domain, where new object is created.
-
Type [Type = UnicodeString]: has “Active Directory Domain Services” value for this event.
Object:
- DN [Type = UnicodeString]: distinguished name of the object that was created.
Note
The LDAP API references an LDAP object by its distinguished name (DN). A DN is a sequence of relative distinguished names (RDN) connected by commas.
An RDN is an attribute with an associated value in the form attribute=value; . These are examples of RDNs attributes:
• DC - domainComponent
• CN - commonName
• OU - organizationalUnitName
• O - organizationName
-
GUID [Type = GUID]: each Active Directory object has globally unique identifier (GUID), which is a 128-bit value that is unique not only in the enterprise but also across the world. GUIDs are assigned to every object created by Active Directory. Each object's GUID is stored in its Object-GUID (objectGUID) property.
Active Directory uses GUIDs internally to identify objects. For example, the GUID is one of an object's properties that is published in the global catalog. Searching the global catalog for a User object's GUID will yield results if the user has an account somewhere in the enterprise. In fact, searching for any object by Object-GUID might be the most reliable way of finding the object you want to find. The values of other object properties can change, but the Object-GUID never changes. When an object is assigned a GUID, it keeps that value for life.
Event Viewer automatically resolves GUID field to real object.
To translate this GUID, use the following procedure:
-
Perform the following LDAP search using LDP.exe tool:
-
Base DN: CN=Schema,CN=Configuration,DC=XXX,DC=XXX
-
Filter: (&(objectClass=*)(objectGUID=GUID))
-
Perform the following operations with the GUID before using it in a search request:
-
We have this GUID to search for: a6b34ab5-551b-4626-b8ee-2b36b3ee6672
-
Take first 3 sections a6b34ab5-551b-4626.
-
For each of these 3 sections you need to change (Invert) the order of bytes, like this b54ab3a6-1b55-2646
-
Add the last 2 sections without transformation: b54ab3a6-1b55-2646-b8ee-2b36b3ee6672
-
Delete - : b54ab3a61b552646b8ee2b36b3ee6672
-
Divide bytes with backslashes: \b5\4a\b3\a6\1b\55\26\46\b8\ee\2b\36\b3\ee\66\72
-
-
Filter example: (&(objectClass=*)(objectGUID = \b5\4a\b3\a6\1b\55\26\46\b8\ee\2b\36\b3\ee\66\72))
-
-
Scope: Subtree
-
Attributes: objectGUID
-
-
-
Class [Type = UnicodeString]: class of the object that was created. Some of the common Active Directory object classes:
-
container – for containers.
-
user – for users.
-
group – for groups.
-
domainDNS – for domain object.
-
groupPolicyContainer – for group policy objects.
For all possible values of this field open Active Directory Schema snap-in (see how to enable this snap-in: https://technet.microsoft.com/library/Cc755885(v=WS.10).aspx) and navigate to Active Directory Schema\Classes. Or use this document: https://msdn.microsoft.com/library/cc221630.aspx
-
Operation:
- Correlation ID [Type = GUID]: multiple modifications are often executed as one operation via LDAP. This value allows you to correlate all the modification events that comprise the operation. Just look for other events from current subcategory with the same Correlation ID, for example “5136: A directory service object was modified.” and “5139: A directory service object was moved.”
Note
GUID is an acronym for 'Globally Unique Identifier'. It is a 128-bit integer number used to identify resources, activities or instances.
- Application Correlation ID [Type = UnicodeString]: always has “-“ value. Not in use.
Security Monitoring Recommendations
For 5137(S): A directory service object was created.
Important
For this event, also see Appendix A: Security monitoring recommendations for many audit events.
-
If you need to monitor creation of Active Directory objects with specific classes, monitor for Class field with specific class name. For example, we recommend that you monitor all new group policy objects creations: groupPolicyContainer class.
-
You must set correct auditing access lists (SACLs) for specific classes within Active Directory container to get 5137. There is no reason to audit all creation events for all types of Active Directory objects; find the most important locations (organizational units, folders, etc.) and monitor for creation of specific classes only (user, computer, group, etc.).