17 KiB
title, description, keywords, ms.prod, ms.mktglfcycl, localizationpriority, author
| title | description | keywords | ms.prod | ms.mktglfcycl | localizationpriority | author |
|---|---|---|---|---|---|---|
| Deploy Device Guard - enable virtualization-based security (Windows 10) | This article describes how to enable virtualization-based security, one of the main features that are part of Device Guard in Windows 10. | virtualization, security, malware | w10 | deploy | high | brianlic-msft |
Deploy Device Guard: enable virtualization-based security
Applies to
- Windows 10
- Windows Server 2016
Hardware-based security features, also called virtualization-based security or VBS, make up a large part of Device Guard security offerings. VBS reinforces the most important feature of Device Guard: configurable code integrity. There are a few steps to configure hardware-based security features in Device Guard:
-
Decide whether to use the procedures in this topic, or to use the Device Guard readiness tool. To enable VBS, you can download and use the hardware readiness tool on the Microsoft Download Center, or follow the procedures in this topic.
-
Verify that hardware and firmware requirements are met. Verify that your client computers possess the necessary hardware and firmware to run these features. A list of requirements for hardware-based security features is available in Hardware, firmware, and software requirements for Device Guard.
-
Enable the necessary Windows features. There are several ways to enable the Windows features required for hardware-based security. You can use the Device Guard and Credential Guard hardware readiness tool, or see the following section, Windows feature requirements for virtualization-based security.
-
Enable additional features as desired. When the necessary Windows features have been enabled, you can enable additional hardware-based security features as desired. You can use the Device Guard and Credential Guard hardware readiness tool, or see Enable virtualization-based security (VBS), later in this topic.
For information about enabling Credential Guard, see Protect derived domain credentials with Credential Guard.
Windows feature requirements for virtualization-based security
In addition to the hardware requirements found in Hardware, firmware, and software requirements for Device Guard, you must enable certain operating system features before you can enable VBS:
-
With Windows 10, version 1607 or Windows Server 2016:
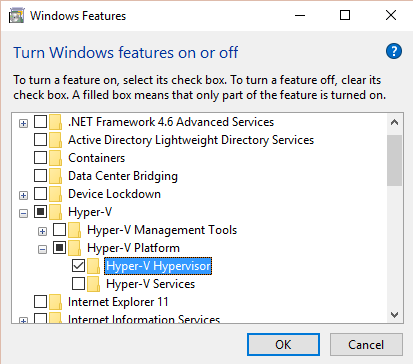
Hyper-V Hypervisor (shown in Figure 1). -
With an earlier version of Windows 10, or Windows Server 2016 Technical Preview 5 or earlier:
Hyper-V Hypervisor and Isolated User Mode (not shown).
Note
You can configure these features manually by using Windows PowerShell or Deployment Image Servicing and Management. For specific information about these methods, see Protect derived domain credentials with Credential Guard.
Figure 1. Enable operating system feature for VBS
After you enable the feature or features, you can enable VBS for Device Guard, as described in the following sections.
Enable Virtualization Based Security (VBS)
Before you begin this process, verify that the target device meets the hardware and firmware requirements for the features that you want, as described in Hardware, firmware, and software requirements for Device Guard. Also, confirm that you have enabled the Windows features discussed in the previous section, Windows feature requirements for virtualization-based security.
There are multiple ways to configure VBS features for Device Guard. You can use the readiness tool rather than the procedures in this topic, or you can use the following procedures, either to configure the appropriate registry keys manually or to use Group Policy.
Important
- The settings in the following procedure include Secure Boot and Secure Boot with DMA. In most situations we recommend that you simply choose Secure Boot. This option provides secure boot with as much protection as is supported by a given computer’s hardware. A computer with input/output memory management units (IOMMUs) will have secure boot with DMA protection. A computer without IOMMUs will simply have secure boot enabled.
In contrast, with Secure Boot with DMA, the setting will enable secure boot—and VBS itself—only on a computer that supports DMA, that is, a computer with IOMMUs. With this setting, any computer without IOMMUs will not have VBS (hardware-based) protection, although it can still have code integrity policies enabled.
For information about how VBS uses the hypervisor to strengthen protections provided by a code integrity policy, see How Device Guard features help protect against threats.- All drivers on the system must be compatible with virtualization-based protection of code integrity; otherwise, your system may fail. We recommend that you enable these features on a group of test computers before you enable them on users' computers.
To configure VBS manually
-
Navigate to the HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceGuard registry subkey.
-
Set the EnableVirtualizationBasedSecurity DWORD value to 1.
-
Set the RequirePlatformSecurityFeatures DWORD value as appropriate:
With Windows 10, version 1607,
or Windows Server 2016With an earlier version of Windows 10,
or Windows Server 2016 Technical Preview 5 or earlier1 enables the Secure Boot option
3 enables the Secure Boot and DMA protection option1 enables the Secure Boot option
2 enables the Secure Boot and DMA protection option -
With a supported operating system earlier than Windows 10, version 1607, or Windows Server 2016, skip this step, and remain in the same registry subkey.
With Windows 10, version 1607, or Windows Server 2016, navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios.
-
Set the HypervisorEnforcedCodeIntegrity DWORD value to 1.
-
Restart the client computer.
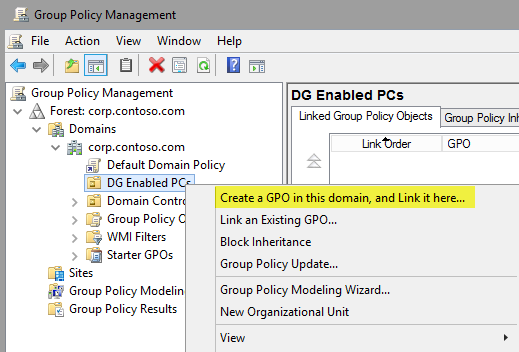
Unfortunately, it would be time consuming to perform these steps manually on every protected computer in your enterprise. Group Policy offers a much simpler way to deploy these features to your organization. This example creates a test organizational unit (OU) called DG Enabled PCs. If you want, you can instead link the policy to an existing OU, and then scope the GPO by using appropriately named computer security groups.
Note
We recommend that you test-enable these features on a group of test computers before you enable them on users' computers. If untested, there is a possibility that this feature can cause system instability and ultimately cause the client operating system to fail.
Use Group Policy to enable VBS
-
To create a new GPO, right-click the OU to which you want to link the GPO, and then click Create a GPO in this domain, and Link it here.
Figure 2. Create a new OU-linked GPO
-
Give the new GPO a name, for example, Contoso VBS settings GPO Test, or any name you prefer. Ideally, the name will align with your existing GPO naming convention.
-
Open the Group Policy Management Editor: right-click the new GPO, and then click Edit.
-
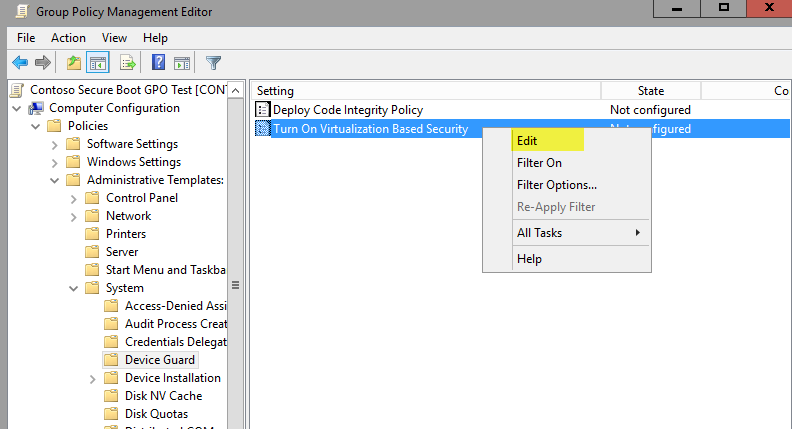
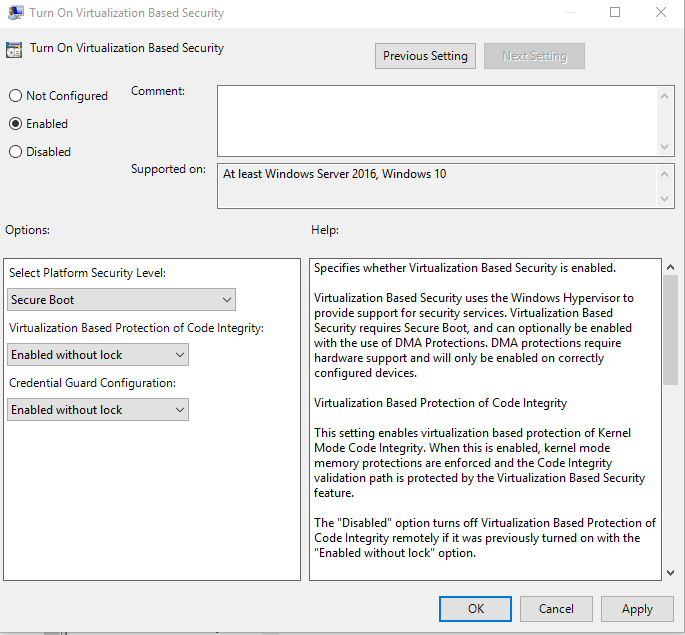
Within the selected GPO, navigate to Computer Configuration\Administrative Templates\System\Device Guard. Right-click Turn On Virtualization Based Security, and then click Edit.
Figure 3. Enable VBS
-
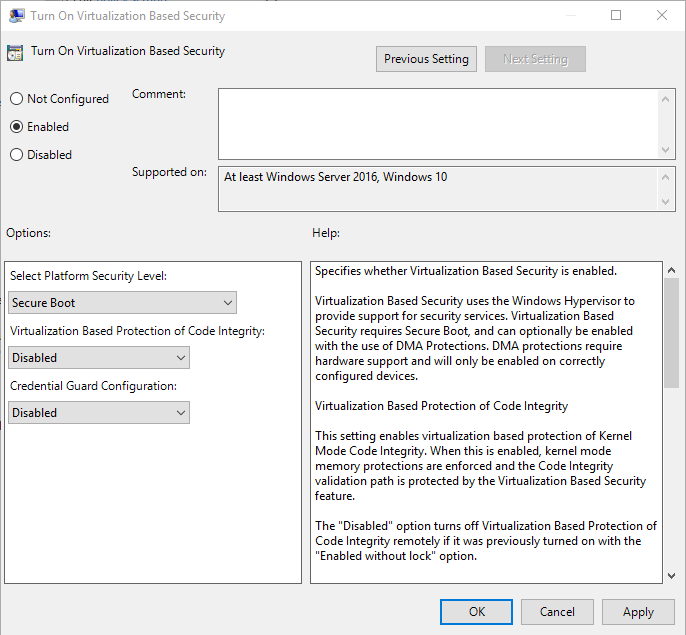
Select the Enabled button, and then choose a secure boot option, such as Secure Boot, from the Select Platform Security Level list.
Figure 4. Configure VBS, Secure Boot setting (in Windows 10, version 1607)
Important
These settings include Secure Boot and Secure Boot with DMA. In most situations we recommend that you choose Secure Boot. This option provides secure boot with as much protection as is supported by a given computer’s hardware. A computer with input/output memory management units (IOMMUs) will have secure boot with DMA protection. A computer without IOMMUs will simply have secure boot enabled.
In contrast, with Secure Boot with DMA, the setting will enable secure boot—and VBS itself—only on a computer that supports DMA, that is, a computer with IOMMUs. With this setting, any computer without IOMMUs will not have VBS (hardware-based) protection, although it can have code integrity policies enabled.
For information about how VBS uses the hypervisor to strengthen protections provided by a code integrity policy, see How Device Guard features help protect against threats. -
For Virtualization Based Protection of Code Integrity, select the appropriate option.
Warning
Virtualization-based protection of code integrity may be incompatible with some devices and applications. We strongly recommend testing this configuration in your lab before enabling virtualization-based protection of code integrity on production systems. Failure to do so may result in unexpected failures up to and including data loss or a blue screen error (also called a stop error).
Select an option as follows:
-
With Windows 10, version 1607 or Windows Server 2016, choose an appropriate option:
For an initial deployment or test deployment, we recommend Enabled without lock.
When your deployment is stable in your environment, we recommend changing to Enabled with lock. This option helps protect the registry from tampering, either through malware or by an unauthorized person. -
With earlier versions of Windows 10, or Windows Server 2016 Technical Preview 5 or earlier:
Select the Enable Virtualization Based Protection of Code Integrity check box.
Figure 5. Configure VBS, Lock setting (in Windows 10, version 1607)
-
-
Close the Group Policy Management Editor, and then restart the Windows 10 test computer. The settings will take effect upon restart.
-
Check the test computer’s event log for Device Guard GPOs.
Processed Device Guard policies are logged in event viewer at Applications and Services Logs\Microsoft\Windows\DeviceGuard-GPEXT\Operational. When the Turn On Virtualization Based Security policy is successfully processed, event ID 7000 is logged, which contains the selected settings within the policy.
Validate enabled Device Guard hardware-based security features
Windows 10 and Windows Server 2016 and later have a WMI class for Device Guard–related properties and features: Win32_DeviceGuard. This class can be queried from an elevated Windows PowerShell session by using the following command:
Get-CimInstance –ClassName Win32_DeviceGuard –Namespace root\Microsoft\Windows\DeviceGuard
Note
The Win32_DeviceGuard WMI class is only available on the Enterprise edition of Windows 10.
The output of this command provides details of the available hardware-based security features as well as those features that are currently enabled. For detailed information about what each property means, refer to Table 1.
Table 1. Win32_DeviceGuard properties
| Properties | Description | Valid values |
|---|---|---|
| AvailableSecurityProperties | This field helps to enumerate and report state on the relevant security properties for Device Guard. |
Note: 4, 5, and 6 were added as of Windows 10, version 1607. |
| InstanceIdentifier | A string that is unique to a particular device. | Determined by WMI. |
| RequiredSecurityProperties | This field describes the required security properties to enable virtualization-based security. |
Note: 4, 5, and 6 were added as of Windows 10, version 1607. |
| SecurityServicesConfigured | This field indicates whether the Credential Guard or HVCI service has been configured. |
|
| SecurityServicesRunning | This field indicates whether the Credential Guard or HVCI service is running. |
|
| Version | This field lists the version of this WMI class. | The only valid value now is 1.0. |
| VirtualizationBasedSecurityStatus | This field indicates whether VBS is enabled and running. |
|
| PSComputerName | This field lists the computer name. | All valid values for computer name. |
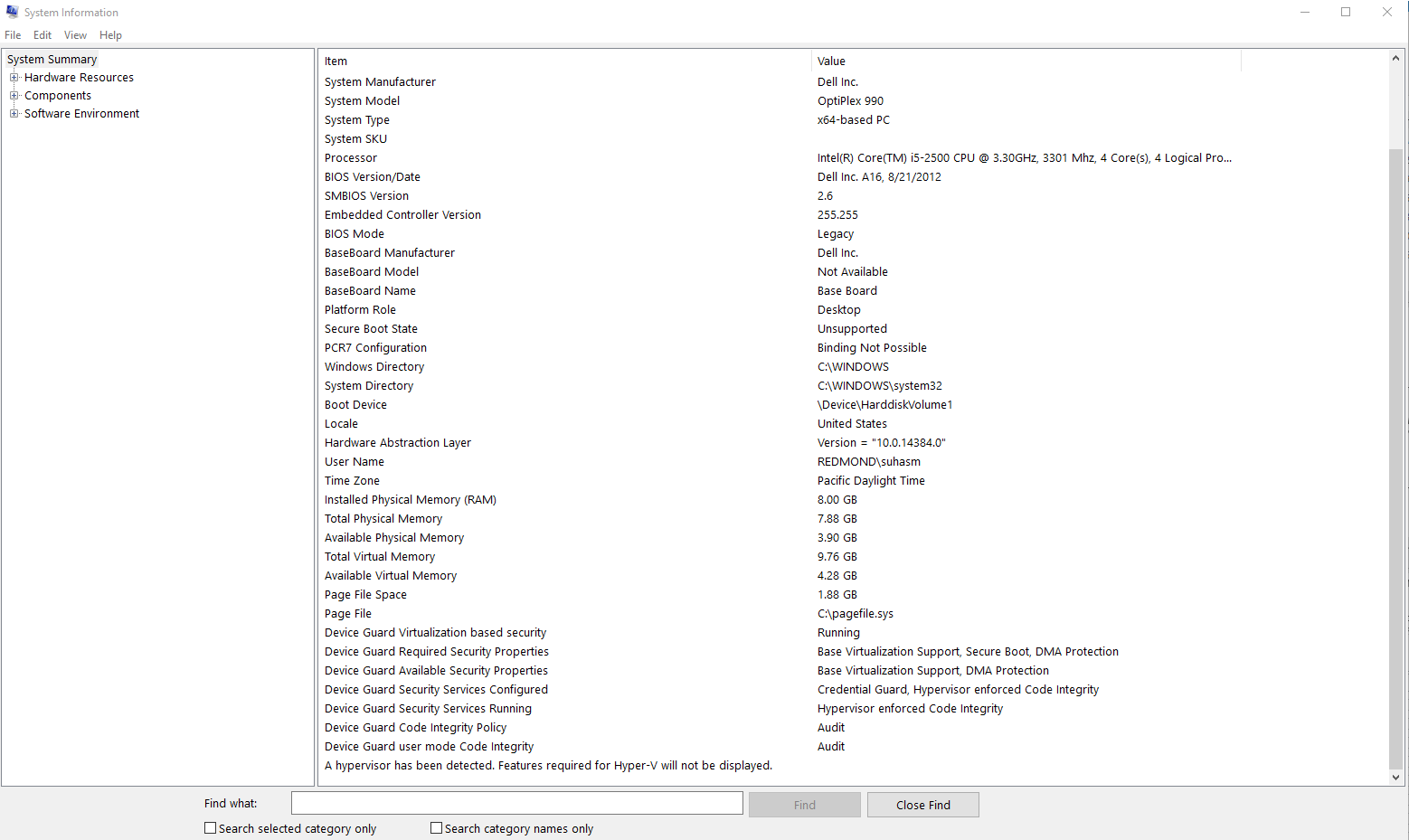
Another method to determine the available and enabled Device Guard features is to run msinfo32.exe from an elevated PowerShell session. When you run this program, the Device Guard properties are displayed at the bottom of the System Summary section, as shown in Figure 6.
Figure 6. Device Guard properties in the System Summary