* Updated deployment-vdi-windows-defender-antivirus.md * Updated deployment-vdi-windows-defender-antivirus.md * Updated deployment-vdi-windows-defender-antivirus.md * updates for new vdi stuff * Adding important note to solve #3493 * Update windows/security/identity-protection/hello-for-business/hello-hybrid-key-whfb-settings-dir-sync.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Typo "<"→"<", ">"→">" https://docs.microsoft.com/en-us/windows/application-management/manage-windows-mixed-reality * Issue #2297 * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Clarification * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * update troubleshoot-np.md * update configure-endpoints-gp.md * Removing a part which is not supported * Name change * update troubleshoot-np.md * removed on-premises added -hello * Added link into Domain controller guide * Line corections * corrected formatting of xml code samples When viewing the page in Win 10/Edge, the xml code samples stretched across the page, running into the side menu. The lack of line breaks also made it hard to read. This update adds line breaks and syntax highlighting, replaces curly double quotes with standard double quotes, and adds a closing tag for <appv:appconnectiongroup>for each code sample * Update windows/security/identity-protection/hello-for-business/hello-identity-verification.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update windows/deployment/update/waas-delivery-optimization-reference.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * corrected formating of XML examples The XML samples here present the same formatting problems as in about-the-connection-group-file51.md (see https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3847/) Perhaps we should open an issue to see if we have more versions of this code sample in the docs * corrected formatting of XML example section In the XML example on this page, the whitespace had been stripped out, so there were no spaces between adjacent attribute values or keys. This made it hard to read, though the original formatting allowed for a scroll bar, so the text was not running into the side of the page (compare to https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3847 and https://github.com/MicrosoftDocs/windows-itpro-docs/pull/3850, where the uncorrected formatting forced the text to run into the side menu). * update configure-endpoints-gp.md * Fixed error in registry path and improved description * Update windows/security/identity-protection/hello-for-business/hello-hybrid-key-whfb-settings-dir-sync.md Co-Authored-By: Trond B. Krokli <38162891+illfated@users.noreply.github.com> * Removing extra line in 25 Suggested by * update windows-analytics-azure-portal.md * re: broken links, credential-guard-considerations Context: * #3513, MVA is being retired and producing broken links * #3860 Microsoft Virtual Academy video links This page contains two links to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course the two links point to is already retired, and no replacement course exists. I removed the first link, as I could not find a similar video available describing which credentials are covered by credential guard. I replaced the second link with a video containing similar material, though it is not a "deep dive". Suggestions on handling this problem, as many pages contain similar links, would be appreciated,. * removed link to retired video re: #3867 Context: * #3513, MVA is being retired and producing broken links * #3867, Microsoft Virtual Academy video links This page contains a broken link to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course is already retired, and no replacement course exists. I removed the whole _See Also_ section, as I could not find a video narrowly or deeply addressing how to protect privelaged users with Credential Guard. The most likely candidate is too short and general: https://www.linkedin.com/learning/cism-cert-prep-1-information-security-governance/privileged-account-management * addressing broken mva links, #3817 Context: * #3513, MVA is being retired and producing broken links * #3817, Another broken link This page contains two links to deprecated video content on Microsoft Virtual Academy (MVA). MVA is being retired. In addition, the Deep Dive course the two links point to is already retired, and no replacement course exists. I removed the first link, as we no longer have a video with similar content for a similar audience. The most likely candidate is https://www.linkedin.com/learning/programming-foundations-web-security-2/types-of-credential-attacks, which is more general and for a less technical audience. I removed the second link and the _See Also_ section, as I could not find a similar video narrowly focused on which credentials are covered by Credential Guard. Most of the related material available now describes how to perform a task. * Update deployment-vdi-windows-defender-antivirus.md * typo fix re: #3876; DMSA -> DSMA * Addressing dead MVA links, #3818 This page, like its fellows in the mva-links label, contains links to a retired video course on a website that is retiring soon. The links listed by the user in issue #3818 were also on several other pages, related to Credentials Guard. These links were addressed in the pull requests #3875, #3872, and #3871 Credentials threat & lateral threat link: removed (see PR #3875 for reasoning) Virtualization link: replaced (see #3871 for reasoning) Credentials protected link: removed (see #3872 for reasoning) * Adding notes for known issue in script Solves #3869 * Updated the download link admx files Windows 10 Added link for April 2018 and Oct 2018 ADMX files. * added event logs path Referenced : https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-defender-exploit-guard/event-views-exploit-guard * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Suggestions applied. Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: JohanFreelancer9 <48568725+JohanFreelancer9@users.noreply.github.com> * Update deployment-vdi-windows-defender-antivirus.md * screenshot update * Add files via upload * update 4 scrrenshots * Update deployment-vdi-windows-defender-antivirus.md * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Update browsers/internet-explorer/ie11-deploy-guide/administrative-templates-and-ie11.md Co-Authored-By: Nicole Turner <39884432+nenonix@users.noreply.github.com> * Re: #3909 Top link is broken, #3909 > The link here does not work: > Applies to: Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP) The link to the pdf describing MDATP was broken. Thankfully, PR #2897 updated the same link in another page some time ago, so I didn't have to go hunting for an equivalent * CI Update * Updated as per task 3405344 * Updated author * Update windows-analytics-azure-portal.md * added the example query * Updated author fields * Update office-csp.md * update video for testing * update video * Update surface-hub-site-readiness-guide.md line 134 Fixed video link MD formatting * fixing video url * updates from Albert * Bulk replaced author to manikadhiman * Bulk replaced ms.author to v-madhi * Latest content is published (#371) * Added 1903 policy DDF link and fixed a typo * Reverted the DDF version * Latest update (#375) * Update deployment-vdi-windows-defender-antivirus.md * Update deployment-vdi-windows-defender-antivirus.md
8.8 KiB
title, description, ms.prod, ms.mktglfcycl, ms.sitesec, author, ms.author, ms.topic, ms.localizationpriority, ms.date, ms.reviewer, manager
| title | description | ms.prod | ms.mktglfcycl | ms.sitesec | author | ms.author | ms.topic | ms.localizationpriority | ms.date | ms.reviewer | manager |
|---|---|---|---|---|---|---|---|---|---|---|---|
| NFC-based device provisioning (Windows 10) | w10 | deploy | library | dansimp | dansimp | article | medium | 07/27/2017 | dansimp |
NFC-based device provisioning
Applies to
- Windows 10 Mobile
Near field communication (NFC) enables Windows 10 Mobile Enterprise and Windows 10 Mobile devices to communicate with an NFC tag or another NFC-enabled transmitting device. Enterprises that do bulk provisioning can use NFC-based device provisioning to provide a provisioning package to the device that's being provisioned. NFC provisioning is simple and convenient and it can easily store an entire provisioning package.
The NFC provisioning option enables the administrator to provide a provisioning package during initial device setup (the out-of-box experience or OOBE phase). Administrators can use the NFC provisioning option to transfer provisioning information to persistent storage by tapping an unprovisioned mobile device to an NFC tag or NFC-enabled device. To use NFC for pre-provisioning a device, you must either prepare your own NFC tags by storing your provisioning package to a tag as described in this section, or build the infrastructure needed to transmit a provisioning package between an NFC-enabled device and a mobile device during OOBE.
Provisioning OOBE UI
All Windows 10 Mobile Enterprise and Windows 10 Mobile images have the NFC provisioning capability incorporated into the operating system. On devices that support NFC and are running Windows 10 Mobile Enterprise or Windows 10 Mobile, NFC-based device provisioning provides an additional mechanism to provision the device during OOBE.
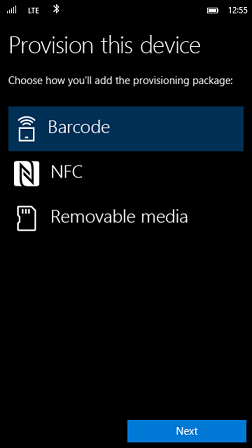
On all Windows devices, device provisioning during OOBE can be triggered by 5 fast taps on the Windows hardware key, which shows the Provision this device screen. In the Provision this device screen, select NFC for NFC-based provisioning.
If there is an error during NFC provisioning, the device will show a message if any of the following errors occur:
- NFC initialization error - This can be caused by any error that occurs before data transfer has started. For example, if the NFC driver isn't enabled or there's an error communicating with the proximity API.
- Interrupted download or incomplete package transfer - This error can happen if the peer device is out of range or the transfer is aborted. This error can be caused whenever the device being provisioned fails to receive the provisioning package in time.
- Incorrect package format - This error can be caused by any protocol error that the operating system encounters during the data transfer between the devices.
- NFC is disabled by policy - Enterprises can use policies to disallow any NFC usage on the managed device. In this case, NFC functionality is not enabled.
NFC tag
You can use an NFC tag for minimal provisioning and use an NFC-enabled device tag for larger provisioning packages.
The protocol used for NFC-based device provisioning is similar to the one used for NFC provisioning on Windows Embedded 8.1 Handheld, which supported both single-chunk and multi-chunk transfer when the total transfer didn't fit in one NDEP message size. In Windows 10, the provisioning stack contains the following changes:
- Protocol namespace - The protocol namespace has changed from Windows.WEH.PreStageProv.Chunk to Windows.ProvPlugins.Chunk.
- Tag data type - The tag data type has changed from UTF-8 into binary raw data.
Note
The NFC tag doesn't go in the secondary device. You can transfer the NFC tag by using a provisioning package from device-to-device using the NFC radio or by re-reading the provisioning package from an NFC tag.
NFC tag components
NFC tags are suitable for very light applications where minimal provisioning is required. The size of NFC tags that contain provisioning packages is typically 4 KB to 10 KB.
To write to an NFC tag, you will need to use an NFC Writer tool, or you can use the ProximityDevice class API to write your own custom tool to transfer your provisioning package file to your NFC tag. The tool must publish a binary message (write) a Chunk data type to your NFC tag.
The following table describes the information that is required when writing to an NFC tag.
| Required field | Description |
|---|---|
| Type | Windows.ProvPlugins.Chunk The receiving device uses this information to understand information in the Data field. |
| Data | Tag data with small header in raw binary format that contains a chunk of the provisioning package to be transferred. |
NFC provisioning helper
The NFC provisioning helper device must split the provisioning package raw content into multiple parts and publish these in order. Each part should follow the following format:
| Version (1 byte) | Leading (1 byte) | Order (1 byte) | Total (1 byte) | Chunk payload (N bytes) |
For each part:
- Version should always be 0x00.
- Leading byte should always be 0xFF.
- Order represents which message chunk (out of the whole message) the part belongs to. The Order begins with zero (0).
- Total represents the total number of chunks to be transferred for the whole message.
- Chunk payload represents each of the split parts.
The NFC provisioning helper device must publish the record in a type of Windows.ProvPlugins.Chunk.
Code example
The following example shows how to write to an NFC tag. This example assumes that the tag is already in range of the writing device.
private async void WriteProvPkgToTag(IStorageFile provPkgFile)
{
var buffer = await FileIO.ReadBufferAsync(provPkgFile);
if (null == buffer)
{
return;
}
var proximityDevice = Windows.Networking.Proximity.ProximityDevice.GetDefault();
if (null == proximityDevice)
{
return;
}
var dataWriter = new DataWriter();
var header = new NfcProvHeader();
header.version = NFC_PROV_MESSAGE_CURRENT_VERSION; // Currently the supported version is 0x00.
header.leading = NFC_PROV_MESSAGE_LEADING_BYTE; // The leading byte should be always 0xFF.
header.index = 0; // Assume we only have 1 chunk.
header.total = 1; // Assume we only have 1 chunk.
// Write the header first and then the raw data of the provisioning package.
dataWriter.WriteBytes(GetBytes(header));
dataWriter.WriteBuffer(buffer);
var chunkPubId = proximityDevice.PublishBinaryMessage(
"Windows:WriteTag.ProvPlugins.Chunk",
dataWriter.DetachBuffer());
}
NFC-enabled device tag components
Provisioning from an NFC-enabled source device allows for larger provisioning packages than can be transferred using an NFC tag. When provisioning from an NFC-enabled device, we recommend that the total file size not exceed 120 KB. Be aware that the larger the NFC file is, the longer it will take to transfer the provisioning file. Depending on your NFC hardware, the transfer time for a 120 KB file will vary between 2.5 seconds and 10 seconds.
To provision from an NFC-enabled source device, use ProximityDevice class API to write your own custom tool that transfers your provisioning package in chunks to your target mobile device. The tool must publish binary messages (transmit) a Header message, followed by one or more Chunk messages. The Header specifies the total amount of data that will be transferred to the target device; the Chunks must contain binary raw data formatted provisioning data, as shown in the NFC tag components section.
For detailed information and code samples on how to implement an NFC-enabled device tag, see ConvertToNfcMessageAsync in this GitHub NfcProvisioner Universal Windows app example. The sample app shows you how to host the provisioning package on a master device so that you can transfer it to the receiving device.