6.2 KiB
title, description, keywords, search.product, ms.pagetype, ms.prod, ms.mktglfcycl, ms.sitesec, ms.pagetype, ms.localizationpriority, author, ms.author, ms.date
| title | description | keywords | search.product | ms.pagetype | ms.prod | ms.mktglfcycl | ms.sitesec | ms.pagetype | ms.localizationpriority | author | ms.author | ms.date |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Enable ASR rules individually to protect your organization | Enable ASR rules to protect your devices from attacks the use macros, scripts, and common injection techniques | Attack surface reduction, hips, host intrusion prevention system, protection rules, anti-exploit, antiexploit, exploit, infection prevention, enable, turn on | eADQiWindows 10XVcnh | security | w10 | manage | library | security | medium | andreabichsel | v-anbic | 06/29/2018 |
Enable Attack surface reduction
Applies to:
- Windows 10, version 1709 and later
- Windows Server 2016
Audience
- Enterprise security administrators
Manageability available with
- Group Policy
- PowerShell
- Configuration service providers for mobile device management
Supported in Windows 10 Enterprise E5, Attack surface reduction is a feature that is part of Windows Defender Exploit Guard. It helps prevent actions and apps that are typically used by exploit-seeking malware to infect machines.
Enable and audit Attack surface reduction rules
You can use Group Policy, PowerShell, or MDM CSPs to configure the state or mode for each rule. This can be useful if you only want to enable some rules, or you want to enable rules individually in audit mode.
For further details on how audit mode works, and when you might want to use it, see the audit Windows Defender Exploit Guard topic.
Attack surface reduction rules are identified by their unique rule ID.
You can manually add the rules by using the GUIDs in the following table:
| Rule description | GUID |
|---|---|
| Block executable content from email client and webmail | BE9BA2D9-53EA-4CDC-84E5-9B1EEEE46550 |
| Block Office applications from creating child processes | D4F940AB-401B-4EFC-AADC-AD5F3C50688A |
| Block Office applications from creating executable content | 3B576869-A4EC-4529-8536-B80A7769E899 |
| Block Office applications from injecting code into other processes | 75668C1F-73B5-4CF0-BB93-3ECF5CB7CC84 |
| Block JavaScript or VBScript from launching downloaded executable content | D3E037E1-3EB8-44C8-A917-57927947596D |
| Block execution of potentially obfuscated scripts | 5BEB7EFE-FD9A-4556-801D-275E5FFC04CC |
| Block Win32 API calls from Office macro | 92E97FA1-2EDF-4476-BDD6-9DD0B4DDDC7B |
| Block executable files from running unless they meet a prevalence, age, or trusted list criteria | 01443614-cd74-433a-b99e-2ecdc07bfc25 |
| Use advanced protection against ransomware | c1db55ab-c21a-4637-bb3f-a12568109d35 |
| Block credential stealing from the Windows local security authority subsystem (lsass.exe) | 9e6c4e1f-7d60-472f-ba1a-a39ef669e4b2 |
| Block process creations originating from PSExec and WMI commands | d1e49aac-8f56-4280-b9ba-993a6d77406c |
| Block untrusted and unsigned processes that run from USB | b2b3f03d-6a65-4f7b-a9c7-1c7ef74a9ba4 |
| Block Office communication applications from creating child processes (available for beta testing) | 26190899-1602-49e8-8b27-eb1d0a1ce869 |
See the Attack surface reduction topic for details on each rule.
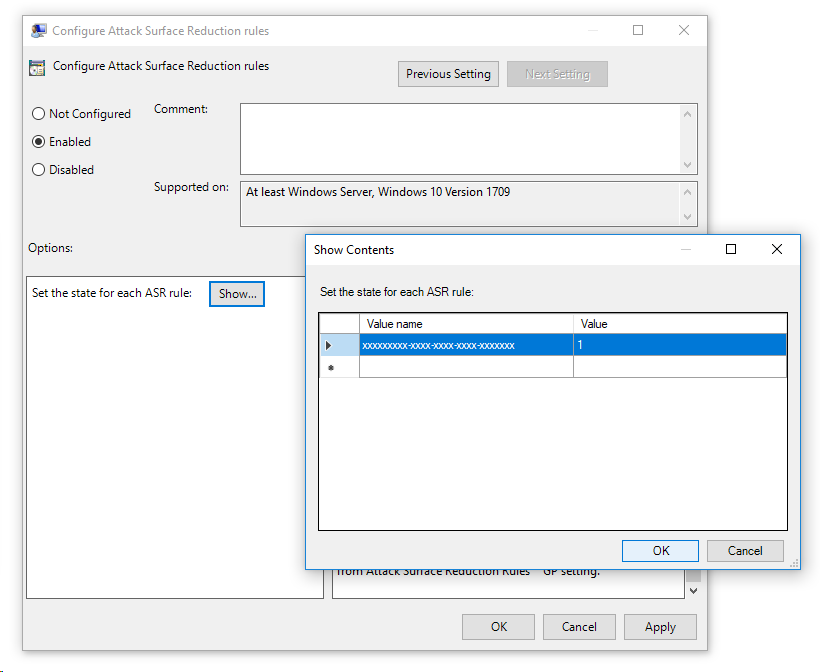
Use Group Policy to enable or audit Attack surface reduction rules
-
On your Group Policy management machine, open the Group Policy Management Console, right-click the Group Policy Object you want to configure and click Edit.
-
In the Group Policy Management Editor go to Computer configuration and click Administrative templates.
-
Expand the tree to Windows components > Windows Defender Antivirus > Windows Defender Exploit Guard > Attack surface reduction.
-
Double-click the Configure Attack surface reduction rules setting and set the option to Enabled. You can then set the individual state for each rule in the options section:
- Click Show... and enter the rule ID in the Value name column and your desired state in the Value column as follows:
- Block mode = 1
- Disabled = 0
- Audit mode = 2
- Click Show... and enter the rule ID in the Value name column and your desired state in the Value column as follows:
Use PowerShell to enable or audit Attack surface reduction rules
-
Type powershell in the Start menu, right click Windows PowerShell and click Run as administrator
-
Enter the following cmdlet:
Set-MpPreference -AttackSurfaceReductionRules_Ids <rule ID> -AttackSurfaceReductionRules_Actions Enabled
You can enable the feature in audit mode using the following cmdlet:
Add-MpPreference -AttackSurfaceReductionRules_Ids <rule ID> -AttackSurfaceReductionRules_Actions AuditMode
Use Disabled insead of AuditMode or Enabled to turn the feature off.
[!IMPORTANT> You must specify the state individually for each rule, but you can combine rules and states in a comma seperated list.
In the following example, the first two rules will be enabled, the third rule will be disabled, and the fourth rule will be enabled in audit mode:
Set-MpPreference -AttackSurfaceReductionRules_Ids <rule ID 1>,<rule ID 2>,<rule ID 3>,<rule ID 4> -AttackSurfaceReductionRules_Actions Enabled, Enabled, Disabled, AuditMode
You can also the Add-MpPreference PowerShell verb to add new rules to the existing list.
Warning
Set-MpPreferencewill always overwrite the existing set of rules. If you want to add to the existing set, you should useAdd-MpPreferenceinstead. You can obtain a list of rules and their current state by usingGet-MpPreference
Use MDM CSPs to enable Attack surface reduction rules
Use the ./Vendor/MSFT/Policy/Config/Defender/AttackSurfaceReductionRules configuration service provider (CSP) to individually enable and set the mode for each rule.