14 KiB
title, description, keywords, search.product, search.appverid, ms.prod, ms.mktglfcycl, ms.sitesec, ms.pagetype, ms.author, author, ms.localizationpriority, manager, audience, ms.collection, ms.topic
| title | description | keywords | search.product | search.appverid | ms.prod | ms.mktglfcycl | ms.sitesec | ms.pagetype | ms.author | author | ms.localizationpriority | manager | audience | ms.collection | ms.topic |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Configure machine proxy and Internet connection settings | Configure the Microsoft Defender ATP proxy and internet settings to enable communication with the cloud service. | configure, proxy, internet, internet connectivity, settings, proxy settings, netsh, winhttp, proxy server | eADQiWindows 10XVcnh | met150 | w10 | deploy | library | security | macapara | mjcaparas | medium | dansimp | ITPro | M365-security-compliance | article |
Configure machine proxy and Internet connectivity settings
Applies to:
Want to experience Microsoft Defender ATP? Sign up for a free trial.
The Microsoft Defender ATP sensor requires Microsoft Windows HTTP (WinHTTP) to report sensor data and communicate with the Microsoft Defender ATP service.
The embedded Microsoft Defender ATP sensor runs in system context using the LocalSystem account. The sensor uses Microsoft Windows HTTP Services (WinHTTP) to enable communication with the Microsoft Defender ATP cloud service.
The WinHTTP configuration setting is independent of the Windows Internet (WinINet) internet browsing proxy settings and can only discover a proxy server by using the following discovery methods:
- Auto-discovery methods:
- Transparent proxy
- Web Proxy Auto-discovery Protocol (WPAD)
Note
If you're using Transparent proxy or WPAD in your network topology, you don't need special configuration settings. For more information on Microsoft Defender ATP URL exclusions in the proxy, see Enable access to Microsoft Defender ATP service URLs in the proxy server.
- Manual static proxy configuration:
- Registry based configuration
- WinHTTP configured using netsh command – Suitable only for desktops in a stable topology (for example: a desktop in a corporate network behind the same proxy)
Configure the proxy server manually using a registry-based static proxy
Configure a registry-based static proxy to allow only Microsoft Defender ATP sensor to report diagnostic data and communicate with Microsoft Defender ATP services if a computer is not be permitted to connect to the Internet.
The static proxy is configurable through Group Policy (GP). The group policy can be found under:
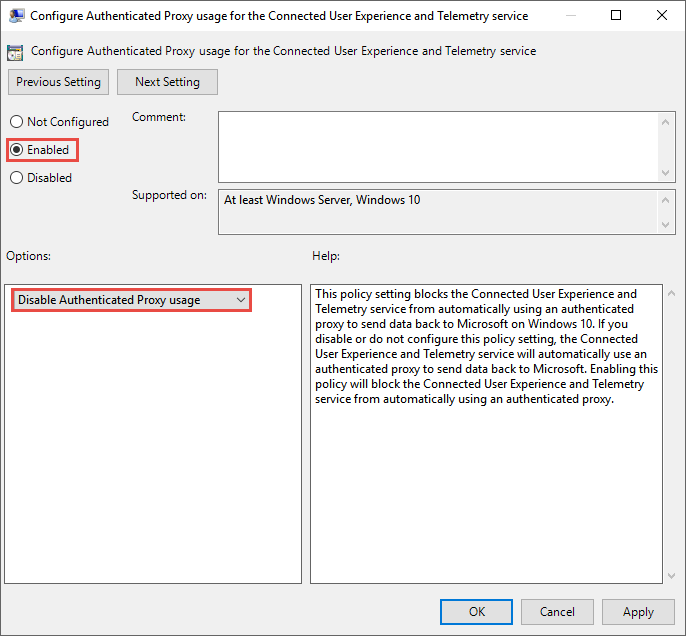
- Administrative Templates > Windows Components > Data Collection and Preview Builds > Configure Authenticated Proxy usage for the Connected User Experience and Telemetry Service
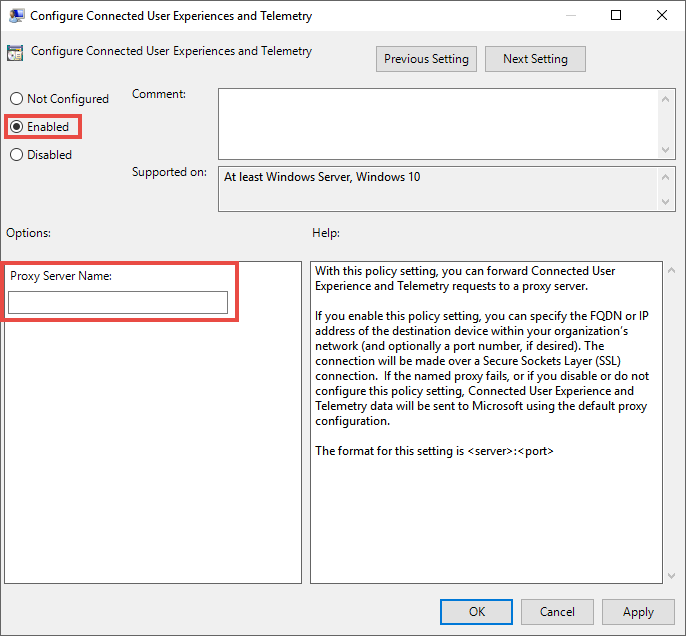
- Administrative Templates > Windows Components > Data Collection and Preview Builds > Configure connected user experiences and telemetry:
-
The policy sets two registry values
TelemetryProxyServeras REG_SZ andDisableEnterpriseAuthProxyas REG_DWORD under the registry keyHKLM\Software\Policies\Microsoft\Windows\DataCollection.The registry value
TelemetryProxyServertakes the following string format:<server name or ip>:<port>For example: 10.0.0.6:8080
The registry value
DisableEnterpriseAuthProxyshould be set to 1.
-
Configure the proxy server manually using netsh command
Use netsh to configure a system-wide static proxy.
Note
- This will affect all applications including Windows services which use WinHTTP with default proxy.
- Laptops that are changing topology (for example: from office to home) will malfunction with netsh. Use the registry-based static proxy configuration.
-
Open an elevated command-line:
a. Go to Start and type cmd.
b. Right-click Command prompt and select Run as administrator.
-
Enter the following command and press Enter:
netsh winhttp set proxy <proxy>:<port>For example: netsh winhttp set proxy 10.0.0.6:8080
To reset the winhttp proxy, enter the following command and press Enter
netsh winhttp reset proxy
See Netsh Command Syntax, Contexts, and Formatting to learn more.
Enable access to Microsoft Defender ATP service URLs in the proxy server
If a proxy or firewall is blocking all traffic by default and allowing only specific domains through or HTTPS scanning (SSL inspection) is enabled, make sure that the following URLs are not blocked by default. Do not disable security monitoring or inspection of these URLs, but allow them as you would other internet traffic. They permit communication with Microsoft Defender ATP service in port 80 and 443:
Note
URLs that include v20 in them are only needed if you have Windows 10, version 1803 or later machines. For example,
us-v20.events.data.microsoft.comis only needed if the machine is on Windows 10, version 1803 or later.
| Service location | Microsoft.com DNS record |
|---|---|
| Common URLs for all locations | *.blob.core.windows.net crl.microsoft.comctldl.windowsupdate.com events.data.microsoft.comnotify.windows.com |
| European Union | eu.vortex-win.data.microsoft.comeu-v20.events.data.microsoft.comwinatp-gw-neu.microsoft.comwinatp-gw-weu.microsoft.com |
| United Kingdom | uk.vortex-win.data.microsoft.com uk-v20.events.data.microsoft.comwinatp-gw-uks.microsoft.comwinatp-gw-ukw.microsoft.com |
| United States | us.vortex-win.data.microsoft.comus-v20.events.data.microsoft.comwinatp-gw-cus.microsoft.com winatp-gw-eus.microsoft.com |
If a proxy or firewall is blocking anonymous traffic, as Microsoft Defender ATP sensor is connecting from system context, make sure anonymous traffic is permitted in the previously listed URLs.
Microsoft Defender ATP service backend IP range
If you network devices don't support the URLs white-listed in the prior section, you can use the following information.
Microsoft Defender ATP is built on Azure cloud, deployed in the following regions:
- +<Region Name="uswestcentral">
- +<Region Name="useast2">
- +<Region Name="useast">
- +<Region Name="europenorth">
- +<Region Name="europewest">
- +<Region Name="uksouth">
- +<Region Name="ukwest">
You can find the Azure IP range on Microsoft Azure Datacenter IP Ranges.
Note
As a cloud-based solution, the IP range can change. It's recommended you move to DNS resolving setting.
Verify client connectivity to Microsoft Defender ATP service URLs
Verify the proxy configuration completed successfully, that WinHTTP can discover and communicate through the proxy server in your environment, and that the proxy server allows traffic to the Microsoft Defender ATP service URLs.
-
Download the connectivity verification tool to the PC where Microsoft Defender ATP sensor is running on.
-
Extract the contents of WDATPConnectivityAnalyzer on the machine.
-
Open an elevated command-line:
a. Go to Start and type cmd.
b. Right-click Command prompt and select Run as administrator.
-
Enter the following command and press Enter:
HardDrivePath\WDATPConnectivityAnalyzer.cmdReplace HardDrivePath with the path where the WDATPConnectivityAnalyzer tool was downloaded to, for example
C:\Work\tools\WDATPConnectivityAnalyzer\WDATPConnectivityAnalyzer.cmd -
Extract the WDATPConnectivityAnalyzerResult.zip file created by tool in the folder used in the HardDrivePath.
-
Open WDATPConnectivityAnalyzer.txt and verify that you have performed the proxy configuration steps to enable server discovery and access to the service URLs.
The tool checks the connectivity of Microsoft Defender ATP service URLs that Microsoft Defender ATP client is configured to interact with. It then prints the results into the WDATPConnectivityAnalyzer.txt file for each URL that can potentially be used to communicate with the Microsoft Defender ATP services. For example:Testing URL : https://xxx.microsoft.com/xxx 1 - Default proxy: Succeeded (200) 2 - Proxy auto discovery (WPAD): Succeeded (200) 3 - Proxy disabled: Succeeded (200) 4 - Named proxy: Doesn't exist 5 - Command line proxy: Doesn't exist
If at least one of the connectivity options returns a (200) status, then the Microsoft Defender ATP client can communicate with the tested URL properly using this connectivity method.
However, if the connectivity check results indicate a failure, an HTTP error is displayed (see HTTP Status Codes). You can then use the URLs in the table shown in Enable access to Microsoft Defender ATP service URLs in the proxy server. The URLs you'll use will depend on the region selected during the onboarding procedure.
Note
The Connectivity Analyzer tool is not compatible with ASR rule Block process creations originating from PSExec and WMI commands. You will need to temporarily disable this rule to run the connectivity tool. When the TelemetryProxyServer is set, in Registry or via Group Policy, Microsoft Defender ATP will fall back to direct if it can't access the defined proxy.
Conduct investigations with Microsoft Defender ATP behind a proxy
Microsoft Defender ATP supports network connection monitoring from different levels of the operating system network stack. A challenging case is when the network uses a forward proxy as a gateway to the internet.
The proxy acts as if it was the target endpoint. In these cases, simple network connection monitors will audit the connections with the proxy which is correct but has lower investigation value. Microsoft Defender ATP supports advanced HTTP level sensor.
By enabling this sensor, Microsoft Defender ATP will expose a new type of events that surfaces the real target domain names.
Investigation Impact
In machine's timeline the IP address will keep representing the proxy, while the real target address shows up.
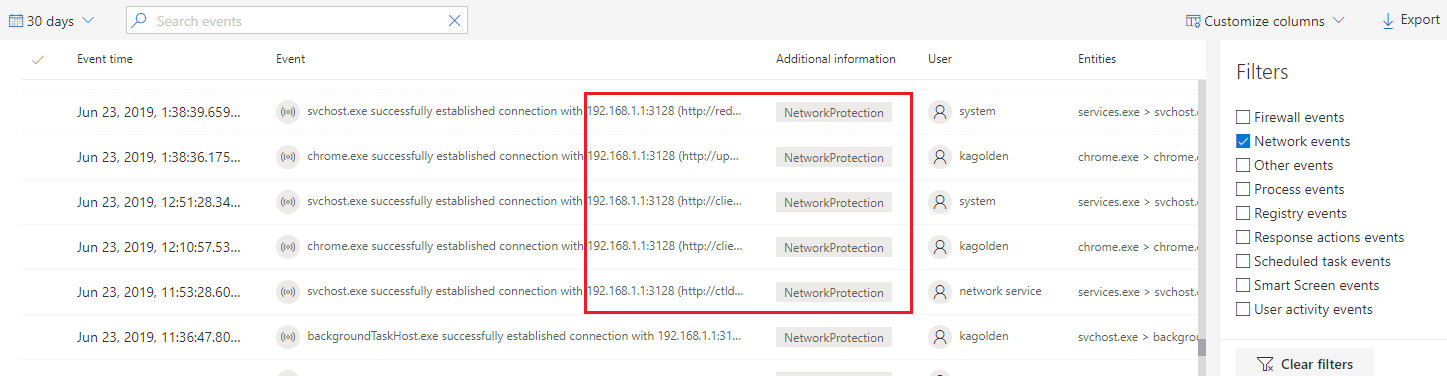
Additional events triggered by the Network Protection layer are now available to surface the real domain names even behind a proxy.
Event's information:
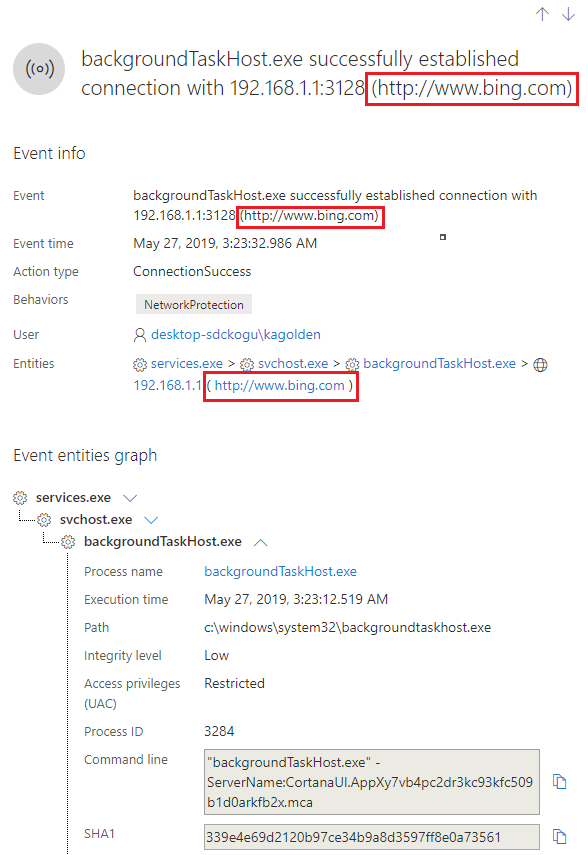
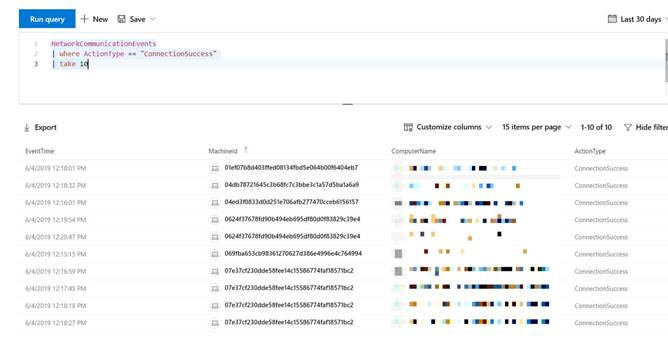
Advanced Hunting
All new connection events are available for you to hunt on through advanced hunting as well. Since these events are connection events, you can find them under the NetworkCommunicationEvents table under the ‘ConnecionSuccess’ action type.
Using this simple query will show you all the relevant events:
NetworkCommunicationEvents
| where ActionType == "ConnectionSuccess"
| take 10
You can also filter out the events that are related to connection to the proxy itself. Use the following query to filter out the connections to the proxy:
NetworkCommunicationEvents
| where ActionType == "ConnectionSuccess" and RemoteIP != "ProxyIP"
| take 10
How to enable the advanced network connection sensor
Monitoring network connection behind forward proxy is possible due to additional Network Events that originate from Network Protection. To see them in machine’s timeline you need to turn Network Protection on at least in audit mode.
Network protection is a feature in Windows Defender Exploit Guard that protects employees using any app from accessing phishing scams, exploit-hosting sites, and malicious content on the Internet. This includes preventing third-party browsers from connecting to dangerous sites. Its behavior can be controlled by the following options: Block and Audit.
If you turn this policy on in "Block" mode, users/apps will be blocked from connecting to dangerous domains. You will be able to see this activity in Windows Defender Security Center.
If you turn this policy on in "Audit" mode, users/apps will not be blocked from connecting to dangerous domains. However, you will still see this activity in Microsoft Defender Security Center.
If you turn this policy off, users/apps will not be blocked from connecting to dangerous domains. You will not see any network activity in Microsoft Defender Security Center.
If you do not configure this policy, network blocking will be disabled by default.
Note
In order to enable Monitoring network connection behind forward proxy and see the domains you will need to enable network protection at least in audit mode.
Additional documentation: