28 KiB
title, ms.reviewer, manager, description, ms.author, ms.topic, ms.prod, ms.technology, author
| title | ms.reviewer | manager | description | ms.author | ms.topic | ms.prod | ms.technology | author |
|---|---|---|---|---|---|---|---|---|
| Policy CSP - DeviceInstallation | dansimp | Policy CSP - DeviceInstallation | v-madhi | article | w10 | windows | v-madhi |
Policy CSP - DeviceInstallation
DeviceInstallation policies
- DeviceInstallation/AllowInstallationOfMatchingDeviceIDs
- DeviceInstallation/AllowInstallationOfMatchingDeviceSetupClasses
- DeviceInstallation/PreventDeviceMetadataFromNetwork
- DeviceInstallation/PreventInstallationOfDevicesNotDescribedByOtherPolicySettings
- DeviceInstallation/PreventInstallationOfMatchingDeviceIDs
- DeviceInstallation/PreventInstallationOfMatchingDeviceSetupClasses
DeviceInstallation/AllowInstallationOfMatchingDeviceIDs
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 5 5 |
 5 5 |
 5 5 |
 5 5 |
[!div class = "checklist"]
- Device
This policy setting allows you to specify a list of Plug and Play hardware IDs and compatible IDs for devices that Windows is allowed to install.
Tip
Use this policy setting only when the "Prevent installation of devices not described by other policy settings" policy setting is enabled. Other policy settings that prevent device installation take precedence over this one.
If you enable this policy setting, Windows is allowed to install or update any device whose Plug and Play hardware ID or compatible ID appears in the list you create, unless another policy setting specifically prevents that installation (for example, the "Prevent installation of devices that match any of these device IDs" policy setting, the "Prevent installation of devices for these device classes" policy setting, or the "Prevent installation of removable devices" policy setting). If you enable this policy setting on a remote desktop server, the policy setting affects redirection of the specified devices from a remote desktop client to the remote desktop server.
If you disable or do not configure this policy setting, and no other policy setting describes the device, the "Prevent installation of devices not described by other policy settings" policy setting determines whether the device can be installed.
Peripherals can be specified by their hardware identity. For a list of common identifier structures, see Device Identifier Formats. Test the configuration prior to rolling it out to ensure it allows the devices expected. Ideally test various instances of the hardware. For example, test multiple USB keys rather than only one.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Allow installation of devices that match any of these device IDs
- GP name: DeviceInstall_IDs_Allow
- GP path: System/Device Installation/Device Installation Restrictions
- GP ADMX file name: deviceinstallation.admx
To enable this policy, use the following SyncML. This example allows Windows to install compatible devices with a device ID of USB\Composite or USB\Class_FF. To configure multiple classes, use  as a delimiter.
<SyncML>
<SyncBody>
<Replace>
<CmdID>$CmdID$</CmdID>
<Item>
<Target>
<LocURI>./Device/Vendor/MSFT/Policy/Config/DeviceInstallation/AllowInstallationOfMatchingDeviceIDs</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">string</Format>
</Meta>
<Data><enabled/><Data id="DeviceInstall_IDs_Allow_List" value="1USB\Composite2USB\Class_FF"/></Data>
</Item>
</Replace>
</SyncBody>
</SyncML>
To verify the policy is applied, check C:\windows\INF\setupapi.dev.log and see if the following is listed near the end of the log:
>>> [Device Installation Restrictions Policy Check]
>>> Section start 2018/11/15 12:26:41.659
<<< Section end 2018/11/15 12:26:41.751
<<< [Exit status: SUCCESS]
DeviceInstallation/AllowInstallationOfMatchingDeviceSetupClasses
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 5 5 |
 5 5 |
 5 5 |
 5 5 |
[!div class = "checklist"]
- Device
This policy setting allows you to specify a list of device setup class globally unique identifiers (GUIDs) for device drivers that Windows is allowed to install.
Tip
Use this policy setting only when the "Prevent installation of devices not described by other policy settings" policy setting is enabled. Other policy settings that prevent device installation take precedence over this one.
If you enable this policy setting, Windows is allowed to install or update device drivers whose device setup class GUIDs appear in the list you create, unless another policy setting specifically prevents installation (for example, the "Prevent installation of devices that match these device IDs" policy setting, the "Prevent installation of devices for these device classes" policy setting, or the "Prevent installation of removable devices" policy setting). If you enable this policy setting on a remote desktop server, the policy setting affects redirection of the specified devices from a remote desktop client to the remote desktop server.
This setting allows device installation based on the serial number of a removable device if that number is in the hardware ID.
If you disable or do not configure this policy setting, and no other policy setting describes the device, the "Prevent installation of devices not described by other policy settings" policy setting determines whether the device can be installed.
Peripherals can be specified by their hardware identity. For a list of common identifier structures, see Device Identifier Formats. Test the configuration prior to rolling it out to ensure it allows the devices expected. Ideally test various instances of the hardware. For example, test multiple USB keys rather than only one.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Allow installation of devices using drivers that match these device setup classes
- GP name: DeviceInstall_Classes_Allow
- GP path: System/Device Installation/Device Installation Restrictions
- GP ADMX file name: deviceinstallation.admx
To enable this policy, use the following SyncML. This example allows Windows to install:
- Floppy Disks, ClassGUID = {4d36e980-e325-11ce-bfc1-08002be10318}
- CD ROMs, ClassGUID = {4d36e965-e325-11ce-bfc1-08002be10318}
- Modems, ClassGUID = {4d36e96d-e325-11ce-bfc1-08002be10318}
Enclose the class GUID within curly brackets {}. To configure multiple classes, use  as a delimiter.
<SyncML>
<SyncBody>
<Replace>
<CmdID>$CmdID$</CmdID>
<Item>
<Target>
<LocURI>./Device/Vendor/MSFT/Policy/Config/DeviceInstallation/AllowInstallationOfMatchingDeviceSetupClasses</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">string</Format>
</Meta>
<Data><enabled/><Data id="DeviceInstall_Classes_Allow_List" value="1{4d36e980-e325-11ce-bfc1-08002be10318}2{4d36e965-e325-11ce-bfc1-08002be10318}3{4d36e96d-e325-11ce-bfc1-08002be10318}"/></Data>
</Item>
</Replace>
</SyncBody>
</SyncML>
To verify the policy is applied, check C:\windows\INF\setupapi.dev.log and see if the following is listed near the end of the log:
>>> [Device Installation Restrictions Policy Check]
>>> Section start 2018/11/15 12:26:41.659
<<< Section end 2018/11/15 12:26:41.751
<<< [Exit status: SUCCESS]
DeviceInstallation/PreventDeviceMetadataFromNetwork
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 5 5 |
 5 5 |
 5 5 |
 5 5 |
[!div class = "checklist"]
- Device
This policy setting allows you to prevent Windows from retrieving device metadata from the Internet.
If you enable this policy setting, Windows does not retrieve device metadata for installed devices from the Internet. This policy setting overrides the setting in the Device Installation Settings dialog box (Control Panel > System and Security > System > Advanced System Settings > Hardware tab).
If you disable or do not configure this policy setting, the setting in the Device Installation Settings dialog box controls whether Windows retrieves device metadata from the Internet.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Prevent device metadata retrieval from the Internet
- GP name: DeviceMetadata_PreventDeviceMetadataFromNetwork
- GP path: System/Device Installation
- GP ADMX file name: DeviceSetup.admx
DeviceInstallation/PreventInstallationOfDevicesNotDescribedByOtherPolicySettings
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 5 5 |
 5 5 |
 5 5 |
 5 5 |
[!div class = "checklist"]
- Device
This policy setting allows you to prevent the installation of devices that are not specifically described by any other policy setting.
If you enable this policy setting, Windows is prevented from installing or updating the device driver for any device that is not described by either the "Allow installation of devices that match any of these device IDs" or the "Allow installation of devices for these device classes" policy setting.
If you disable or do not configure this policy setting, Windows is allowed to install or update the device driver for any device that is not described by the "Prevent installation of devices that match any of these device IDs," "Prevent installation of devices for these device classes," or "Prevent installation of removable devices" policy setting.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Prevent installation of devices not described by other policy settings
- GP name: DeviceInstall_Unspecified_Deny
- GP path: System/Device Installation/Device Installation Restrictions
- GP ADMX file name: deviceinstallation.admx
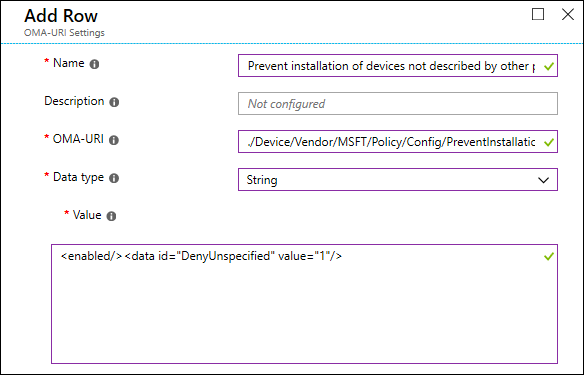
To enable this policy, use the following SyncML. This example prevents Windows from installing devices that are not specifically described by any other policy setting.
<SyncML>
<SyncBody>
<Replace>
<CmdID>$CmdID$</CmdID>
<Item>
<Target>
<LocURI>./Device/Vendor/MSFT/Policy/Config/DeviceInstallation/PreventInstallationOfDevicesNotDescribedByOtherPolicySettings</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">string</Format>
</Meta>
<Data><enabled/><data id="DenyUnspecified" value="1"/></Data>
</Item>
</Replace>
</SyncBody>
</SyncML>
To verify the policy is applied, check C:\windows\INF\setupapi.dev.log and see if the following is listed near the end of the log:
>>> [Device Installation Restrictions Policy Check]
>>> Section start 2018/11/15 12:26:41.659
<<< Section end 2018/11/15 12:26:41.751
<<< [Exit status: SUCCESS]
You can also block installation by using a custom profile in Intune.
DeviceInstallation/PreventInstallationOfMatchingDeviceIDs
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 |
 |
 |
 |
 |
 |
[!div class = "checklist"]
- Device
This policy setting allows you to specify a list of Plug and Play hardware IDs and compatible IDs for devices that Windows is prevented from installing. This policy setting takes precedence over any other policy setting that allows Windows to install a device.
If you enable this policy setting, Windows is prevented from installing a device whose hardware ID or compatible ID appears in the list you create. If you enable this policy setting on a remote desktop server, the policy setting affects redirection of the specified devices from a remote desktop client to the remote desktop server.
If you disable or do not configure this policy setting, devices can be installed and updated as allowed or prevented by other policy settings.
Peripherals can be specified by their hardware identity. For a list of common identifier structures, see Device Identifier Formats. Test the configuration prior to rolling it out to ensure it blocks the devices expected. Ideally test various instances of the hardware. For example, test multiple USB keys rather than only one.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Prevent installation of devices that match any of these device IDs
- GP name: DeviceInstall_IDs_Deny
- GP path: System/Device Installation/Device Installation Restrictions
- GP ADMX file name: deviceinstallation.admx
To enable this policy, use the following SyncML. This example prevents Windows from installing compatible devices with a device ID of USB\Composite or USB\Class_FF. To configure multiple classes, use `` as a delimiter. To apply the policy to matching device classes that are already installed, set DeviceInstall_IDs_Deny_Retroactive to true.
<SyncML>
<SyncBody>
<Replace>
<CmdID>$CmdID$</CmdID>
<Item>
<Target>
<LocURI>./Device/Vendor/MSFT/Policy/Config/DeviceInstallation/PreventInstallationOfMatchingDeviceIDs</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">string</Format>
</Meta>
<Data><enabled/><data id="DeviceInstall_IDs_Deny_Retroactive" value="true"/><Data id="DeviceInstall_IDs_Deny_List" value="1USB\Composite2USB\Class_FF"/></Data>
</Item>
</Replace>
</SyncBody>
</SyncML>
To verify the policy is applied, check C:\windows\INF\setupapi.dev.log and see if the following is listed near the end of the log:
>>> [Device Installation Restrictions Policy Check]
>>> Section start 2018/11/15 12:26:41.659
<<< Section end 2018/11/15 12:26:41.751
<<< [Exit status: SUCCESS]
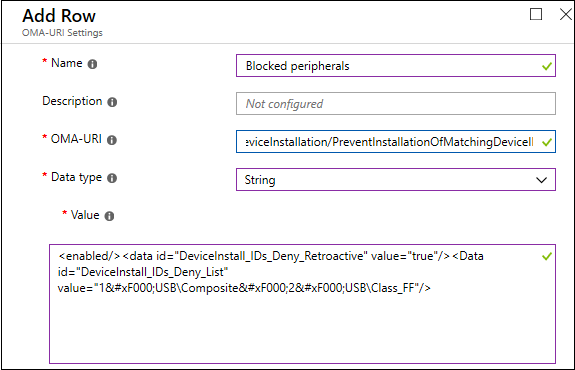
You can also block installation and usage of prohibited peripherals by using a custom profile in Intune.
For example, this custom profile blocks installation and usage of USB devices with hardware IDs "USB\Composite" and "USB\Class_FF", and applies to USB devices with matching hardware IDs that are already installed.
DeviceInstallation/PreventInstallationOfMatchingDeviceSetupClasses
| Home | Pro | Business | Enterprise | Education | Mobile | Mobile Enterprise |
|---|---|---|---|---|---|---|
 |
 |
 |
 |
 |
 |
 |
[!div class = "checklist"]
- Device
This policy setting allows you to specify a list of device setup class globally unique identifiers (GUIDs) for device drivers that Windows is prevented from installing. This policy setting takes precedence over any other policy setting that allows Windows to install a device.
If you enable this policy setting, Windows is prevented from installing or updating device drivers whose device setup class GUIDs appear in the list you create. If you enable this policy setting on a remote desktop server, the policy setting affects redirection of the specified devices from a remote desktop client to the remote desktop server.
If you disable or do not configure this policy setting, Windows can install and update devices as allowed or prevented by other policy settings.
Peripherals can be specified by their hardware identity. For a list of common identifier structures, see Device Identifier Formats. Test the configuration prior to rolling it out to ensure it blocks the devices expected. Ideally test various instances of the hardware. For example, test multiple USB keys rather than only one.
Tip
This is an ADMX-backed policy and requires a special SyncML format to enable or disable. For details, see Understanding ADMX-backed policies.
You must specify the data type in the SyncML as <Format>chr</Format>. For an example SyncML, refer to Enabling a policy.
The payload of the SyncML must be XML-encoded; for this XML encoding, there are a variety of online encoders that you can use. To avoid encoding the payload, you can use CDATA if your MDM supports it. For more information, see CDATA Sections.
ADMX Info:
- GP English name: Prevent installation of devices using drivers that match these device setup classes
- GP name: DeviceInstall_Classes_Deny
- GP path: System/Device Installation/Device Installation Restrictions
- GP ADMX file name: deviceinstallation.admx
To enable this policy, use the following SyncML. This example prevents Windows from installing:
- Floppy Disks, ClassGUID = {4d36e980-e325-11ce-bfc1-08002be10318}
- CD ROMs, ClassGUID = {4d36e965-e325-11ce-bfc1-08002be10318}
- Modems, ClassGUID = {4d36e96d-e325-11ce-bfc1-08002be10318}
Enclose the class GUID within curly brackets {}. To configure multiple classes, use  as a delimiter. To apply the policy to matching device classes that are already installed, set DeviceInstall_Classes_Deny_Retroactive to true.
<SyncML>
<SyncBody>
<Replace>
<CmdID>$CmdID$</CmdID>
<Item>
<Target>
<LocURI>./Device/Vendor/MSFT/Policy/Config/DeviceInstallation/PreventInstallationOfMatchingDeviceSetupClasses</LocURI>
</Target>
<Meta>
<Format xmlns="syncml:metinf">string</Format>
</Meta>
<Data><enabled/><data id="DeviceInstall_Classes_Deny_Retroactive" value="true"/><Data id="DeviceInstall_Classes_Deny_List" value="1{4d36e980-e325-11ce-bfc1-08002be10318}2{4d36e965-e325-11ce-bfc1-08002be10318}3{4d36e96d-e325-11ce-bfc1-08002be10318}"/></Data>
</Item>
</Replace>
</SyncBody>
</SyncML>
To verify the policy is applied, check C:\windows\INF\setupapi.dev.log and see if the following is listed near the end of the log:
>>> [Device Installation Restrictions Policy Check]
>>> Section start 2018/11/15 12:26:41.659
<<< Section end 2018/11/15 12:26:41.751
<<< [Exit status: SUCCESS]
Footnote:
- 1 - Added in Windows 10, version 1607.
- 2 - Added in Windows 10, version 1703.
- 3 - Added in Windows 10, version 1709.
- 4 - Added in Windows 10, version 1803.
- 5 - Added in Windows 10, version 1809.
- 6 - Added in the next major release of Windows 10.